Global Attack Surface Management Market Outlook to 2030
Region:Global
Author(s):Yogita Sahu
Product Code:KROD8746
December 2024
84
About the Report
Global Attack Surface Management Market Overview
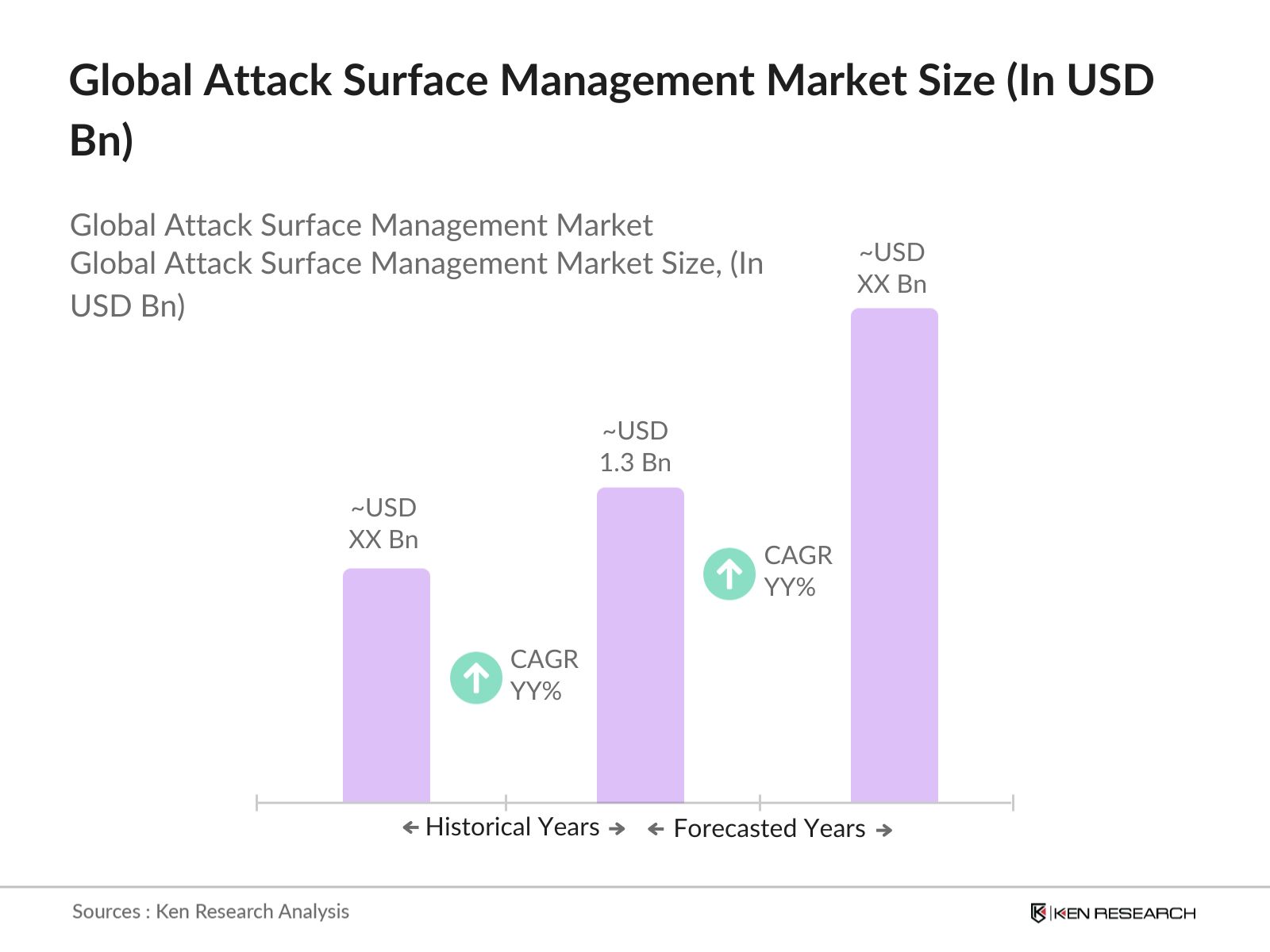
- The Global Attack Surface Management (ASM) market is valued at USD 1.3 billion, according to industry reports, and this growth is driven by the proliferation of connected devices, cloud adoption, and AI-based security measures. As organizations expand their digital footprints, the attack surfaces are growing, which necessitates effective solutions to monitor, manage, and mitigate potential vulnerabilities.
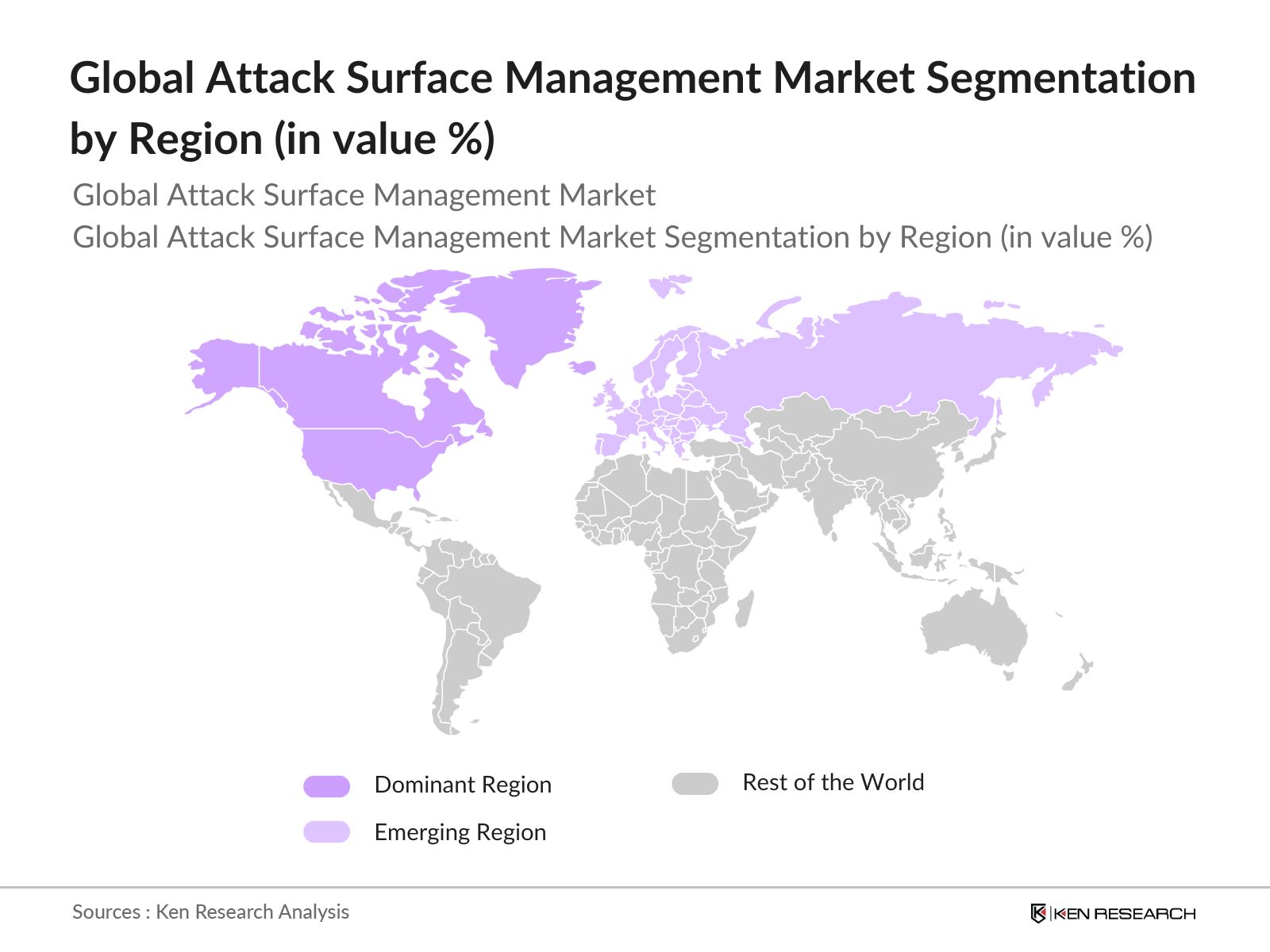
- The market dominance is led by regions such as North America and Europe, where cybersecurity regulations and increased awareness of the importance of ASM are prevalent. In North America, the U.S. leads due to its advanced infrastructure and large-scale adoption of IoT and cloud technologies, which increases exposure to cyber threats.
- The European Union has launched a series of cybersecurity programs to combat increasing cyber threats. By 2024, over $3 billion has been allocated to improve attack surface monitoring technologies for public and private sectors. The EUs Cybersecurity Strategy for the Digital Decade highlights the importance of monitoring attack surfaces, particularly in high-risk sectors such as finance and energy.
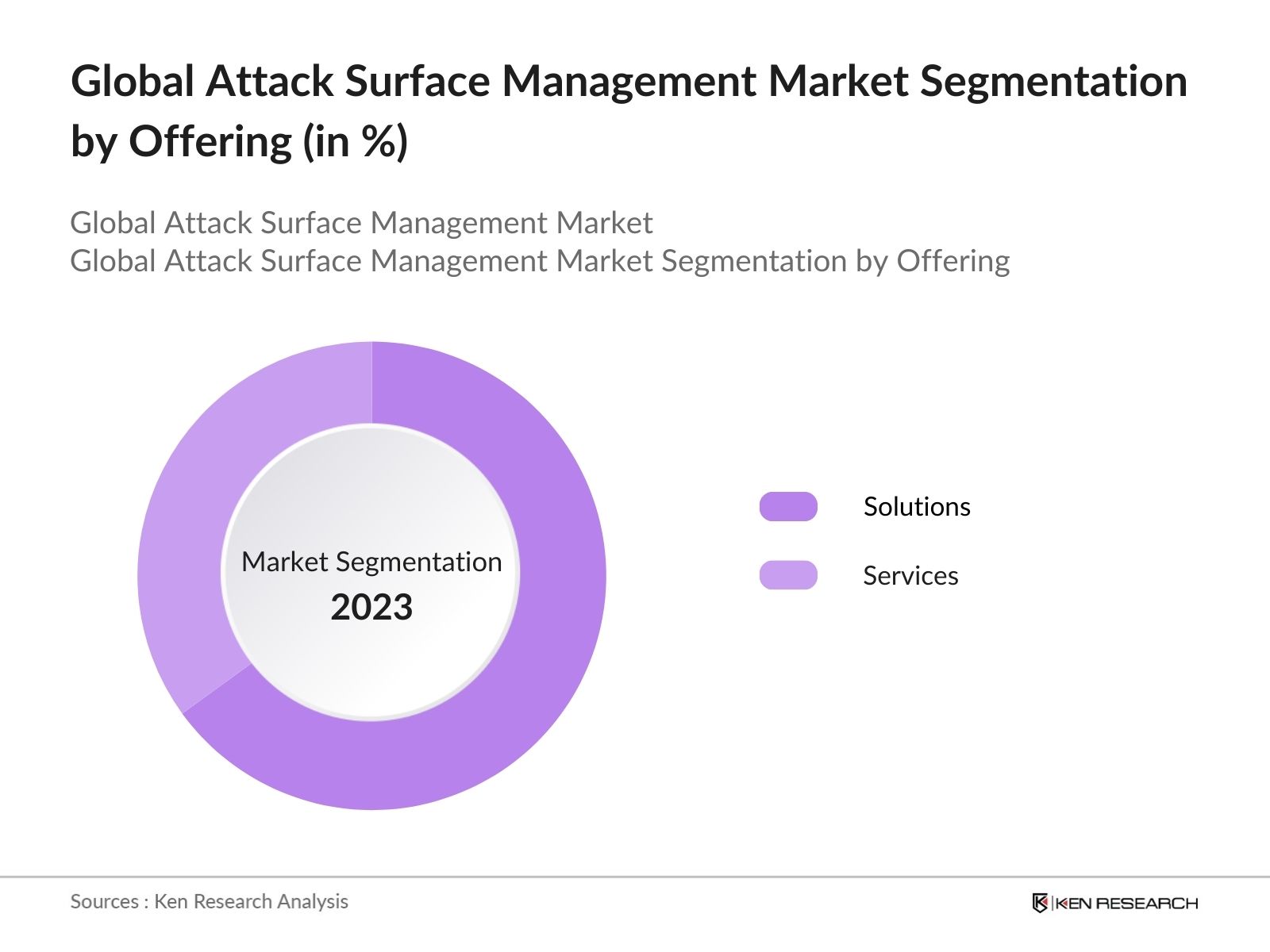
Global Attack Surface Management Market Segmentation
By Offering: The market is segmented into Solutions and Services. Solutions include advanced vulnerability detection tools, continuous monitoring platforms, and attack surface reduction technologies. Services encompass managed security offerings, consulting services, and penetration testing, which are gaining traction due to increased reliance on third-party experts for comprehensive security strategies.
By Deployment Mode: The deployment mode in this market is categorized into Cloud and On-Premises. Cloud deployment is rapidly growing due to the flexibility, scalability, and cost-effectiveness of cloud services. However, on-premises solutions still dominate in industries with stringent security requirements, such as government and defense, where sensitive data needs direct oversight and control.
By Region: The market is segmented into North America, Europe, Asia-Pacific, Latin America, and the Middle East & Africa. North America holds the largest market share, driven by the U.S.'s focus on improving cybersecurity frameworks. Meanwhile, Asia-Pacific is expected to experience the fastest growth, attributed to increased digitalization efforts in China, India, and Japan.
Global Attack Surface Management Market Competitive Landscape
The market is highly competitive, with key players focusing on strategic acquisitions, product launches, and partnerships to strengthen their market positions. Companies like Microsoft, Palo Alto Networks, and IBM are major players dominating the global market.
|
Company |
Year of Establishment |
Headquarters |
Number of Employees |
Revenue (2023) |
Products Offered |
Key Market |
Recent Acquisition |
|
Palo Alto Networks |
2005 |
USA |
|||||
|
Microsoft |
1975 |
USA |
|||||
|
IBM Corporation |
1911 |
USA |
|||||
|
Cisco Systems |
1984 |
USA |
|||||
|
CrowdStrike |
2011 |
USA |
Global Attack Surface Management Market Analysis
Market Growth Drivers
- Increasing Cyber Attacks Across Critical Infrastructure Sectors: In 2024, cyber threats have escalated across various critical infrastructure sectors, including healthcare, energy, and finance. The number of ransomware attacks alone has surged globally, with over 236 million cases reported in the first half of 2024. This growing frequency of cyber-attacks, costing governments and businesses over $4 trillion in damages, is driving the demand for Attack Surface Management (ASM) solutions to detect vulnerabilities before exploitation.
- Increased Cloud Adoption Leading to Expanding Attack Surfaces: The widespread adoption of cloud services by enterprises is increasing their digital footprints, resulting in expanded attack surfaces. By mid-2024, more than 50 million new workloads are expected to be deployed in cloud environments. The rapid shift toward multi-cloud environments among Fortune 500 companies means there are more potential vulnerabilities to monitor and mitigate.
- Surging Regulations for Data Privacy and Cybersecurity Compliance: Governments worldwide are implementing more stringent cybersecurity and data protection regulations to mitigate risks posed by expanding attack surfaces. The introduction of regulations like the Data Protection Law in China and updates to GDPR across Europe has pushed enterprises to ensure compliance, creating demand for sophisticated ASM tools to manage vulnerabilities.
Market Challenges
- High Initial Investment and Implementation Costs: Implementing robust ASM solutions comes with substantial costs, including the purchase of software licenses, integration expenses, and ongoing maintenance. In 2024, the average enterprise spent over $250,000 on initial ASM implementations. These high costs deter small and medium-sized enterprises (SMEs), which often operate on limited cybersecurity budgets, from adopting these solutions, thereby slowing market penetration in this sector.
- Fragmented Technology Landscape and Vendor Solutions: The ASM market is highly fragmented, with numerous vendors offering varying solutions that often lack interoperability. In 2024, over 400 ASM vendors operate globally, leading to confusion among enterprises seeking comprehensive attack surface solutions. The lack of standardized platforms and integration issues between various tools hampers the effectiveness of ASM solutions and adds complexity to their implementation and operation.
Global Attack Surface Management Market Future Outlook
Over the next five years, the Global Attack Surface Management industry is expected to grow. This growth will be driven by factors such as increased digital transformation, especially in emerging markets, the integration of AI and machine learning into cybersecurity solutions.
Future Market Opportunities
- Increased Focus on ASM for IoT Devices: With over 125 billion IoT devices expected to be operational by 2028, ASM solutions will increasingly target this sector, providing specialized vulnerability management tools for connected devices. This trend will be driven by the need to secure IoT ecosystems across industries such as healthcare, automotive, and smart cities.
- Rising Demand for Managed ASM Services Among SMEs: SMEs are expected to increasingly rely on managed ASM services to secure their digital infrastructures. By 2028, the number of SMEs adopting managed cybersecurity services is estimated to grow by over 300,000, with a portion opting for ASM platforms.
Scope of the Report
|
By Offering |
Solutions Services |
|
By Deployment Mode |
Cloud On-Premises |
|
By Organization Size |
Large Enterprises SMEs |
|
By End-User Industry |
BFSI Healthcare IT & Telecom Government & Defense Retail and E-Commerce |
|
By Region |
North America Europe Asia Pacific Latin America Middle East & Africa |
Products
Key Target Audience Organizations and Entities Who Can Benefit by Subscribing This Report:
Government and regulatory bodies (NIST, GDPR compliance authorities)
Financial institutions and BFSI sector
Banks and Financial Institution
Healthcare Companies
IT and telecommunications companies
Energy and utility companies
Retail and e-commerce businesses
Large enterprises and SMEs
Investor and venture capitalist firms
Companies
Players Mentioned in the Report:
Palo Alto Networks
Microsoft Corporation
IBM Corporation
Tenable Inc.
CrowdStrike
Cisco Systems
Trend Micro
CyberArk Software Ltd.
Mandiant (FireEye)
Rapid7
Table of Contents
1. Global Attack Surface Management Market Overview
1.1. Definition and Scope
1.2. Market Taxonomy
1.3. Market Growth Rate
1.4. Market Segmentation Overview
2. Global Attack Surface Management Market Size (In USD Bn)
2.1. Historical Market Size
2.2. Year-On-Year Growth Analysis
2.3. Key Market Developments and Milestones
3. Global Attack Surface Management Market Analysis
3.1. Growth Drivers (increased IoT integration, AI/ML adoption, rising cyberattacks)
3.1.1. IoT Devices Growth
3.1.2. AI and Machine Learning Applications
3.1.3. Expansion of Cyber-Physical Systems
3.1.4. Cloud Infrastructure Adoption
3.2. Market Challenges (complexity of digital ecosystems, integration with legacy systems)
3.2.1. Legacy System Integration
3.2.2. Real-Time Threat Monitoring
3.2.3. Cost of Continuous Management
3.2.4. Regulatory Compliance Challenges
3.3. Opportunities (growing demand for proactive threat management solutions)
3.3.1. AI-Driven Predictive Analysis
3.3.2. Real-Time Risk Monitoring Tools
3.3.3. Cross-Sector Collaboration
3.3.4. Third-Party and Supply Chain Vulnerability Monitoring
3.4. Trends (zero trust architecture, external attack surface management)
3.4.1. Zero Trust Implementation
3.4.2. EASM Adoption
3.4.3. Automated Vulnerability Scanning
3.4.4. Integrated Threat Intelligence
3.5. Government Regulations (GDPR, NIS2, U.S. cybersecurity frameworks)
3.5.1. GDPR Compliance Requirements
3.5.2. U.S. National Cybersecurity Strategy
3.5.3. Regional Cybersecurity Legislation
3.5.4. ISO/IEC Standards for ASM
3.6. SWOT Analysis
3.7. Stakeholder Ecosystem
3.8. Porters Five Forces
3.9. Competition Ecosystem
4. Global Attack Surface Management Market Segmentation
4.1. By Offering (In Value %)
4.1.1. Solutions
4.1.2. Services
4.2. By Deployment Mode (In Value %)
4.2.1. Cloud
4.2.2. On-Premises
4.3. By Organization Size (In Value %)
4.3.1. Large Enterprises
4.3.2. Small and Medium Enterprises (SMEs)
4.4. By End-User Industry (In Value %)
4.4.1. BFSI
4.4.2. Healthcare
4.4.3. IT & Telecom
4.4.4. Government & Defense
4.4.5. Retail and E-Commerce
4.5. By Region (In Value %)
4.5.1. North America
4.5.2. Europe
4.5.3. Asia Pacific
4.5.4. Latin America
4.5.5. Middle East & Africa
5. Global Attack Surface Management Market Competitive Analysis
5.1 Detailed Profiles of Major Companies
5.1.1. Palo Alto Networks
5.1.2. Microsoft Corporation
5.1.3. IBM Corporation
5.1.4. Cisco Systems
5.1.5. Qualys Inc.
5.1.6. Tenable Inc.
5.1.7. CrowdStrike
5.1.8. Trend Micro
5.1.9. Rapid7
5.1.10. CyberArk Software Ltd.
5.1.11. Mandiant (FireEye)
5.1.12. Edgio
5.1.13. Claroty
5.1.14. Axonius
5.1.15. Ivanti
5.2 Cross Comparison Parameters (Offering Type, Deployment, Revenue, Recent Strategic Moves, Headquarters)
5.3 Market Share Analysis
5.4 Strategic Initiatives (Partnerships, Mergers, and Acquisitions)
5.5 Mergers and Acquisitions
5.6 Investment and Funding Analysis
6. Global Attack Surface Management Market Regulatory Framework
6.1. International Standards for Cybersecurity (ISO, NIST)
6.2. Regional Regulatory Requirements (GDPR, NIS Directive)
6.3. Compliance and Audit Mechanisms
6.4. Certification and Risk Assessment
7. Global Attack Surface Management Future Market Size (In USD Bn)
7.1. Future Market Size Projections
7.2. Key Factors Driving Future Growth
8. Global Attack Surface Management Future Market Segmentation
8.1. By Offering
8.2. By Deployment Mode
8.3. By Organization Size
8.4. By End-User Industry
8.5. By Region
9. Global Attack Surface Management Market Analysts Recommendations
9.1. TAM/SAM/SOM Analysis
9.2. Security Posture Optimization
9.3. Expansion Strategies in Emerging Markets
9.4. White Space Opportunity Analysis
Contact US
Research Methodology
Step 1: Identification of Key Variables
The initial phase involves mapping the entire ASM market landscape, identifying key stakeholders, and gathering secondary data from proprietary and public databases to pinpoint the crucial variables affecting the market.
Step 2: Market Analysis and Construction
Historical data is analyzed to build the foundational market structure, incorporating variables such as market penetration, revenue generation, and service providers. This step also involves evaluating the market's regional split and its dynamics across different verticals.
Step 3: Hypothesis Validation and Expert Consultation
Market hypotheses are validated by conducting interviews with industry experts using structured methodologies. These insights are cross-referenced with existing data to provide a well-rounded perspective on market trends and competitive dynamics.
Step 4: Research Synthesis and Final Output
The final stage synthesizes the validated insights and data, culminating in the detailed report. This includes the analysis of product segments, consumer preferences, and market growth strategies.
Frequently Asked Questions
01. How big is the Global Attack Surface Management Market?
The Global Attack Surface Management market is valued at USD 1.3 billion, driven by increasing digital infrastructure, cloud adoption, and rising cyber threats across industries.
02. What are the key challenges in the Global Attack Surface Management Market?
Key challenges in the Global Attack Surface Management market include managing complex digital ecosystems, ensuring compliance with evolving regulations, and securing interconnected cloud and IoT devices against a growing array of cyber threats.
03. Who are the major players in the Global Attack Surface Management Market?
Major players in the Global Attack Surface Management market include Palo Alto Networks, Microsoft, IBM, Tenable Inc., and CrowdStrike, who lead the market with innovative products and strategic partnerships.
04. What drives the Global Attack Surface Management Market?
The Global Attack Surface Management market is driven by the rising adoption of IoT devices, cloud computing, AI-powered security solutions, and the increasing sophistication of cyber-attacks, requiring proactive threat management.
05. What sectors are the key end-users of Attack Surface Management Solutions?
Key sectors include BFSI, healthcare, government and defense, IT & telecom, and energy & utilities, where robust cybersecurity is critical for operational continuity.
Why Buy From Us?

What makes us stand out is that our consultants follows Robust, Refine and Result (RRR) methodology. i.e. Robust for clear definitions, approaches and sanity checking, Refine for differentiating respondents facts and opinions and Result for presenting data with story

We have set a benchmark in the industry by offering our clients with syndicated and customized market research reports featuring coverage of entire market as well as meticulous research and analyst insights.

While we don't replace traditional research, we flip the method upside down. Our dual approach of Top Bottom & Bottom Top ensures quality deliverable by not just verifying company fundamentals but also looking at the sector and macroeconomic factors.

With one step in the future, our research team constantly tries to show you the bigger picture. We help with some of the tough questions you may encounter along the way: How is the industry positioned? Best marketing channel? KPI's of competitors? By aligning every element, we help maximize success.

Our report gives you instant access to the answers and sources that other companies might choose to hide. We elaborate each steps of research methodology we have used and showcase you the sample size to earn your trust.

If you need any support, we are here! We pride ourselves on universe strength, data quality, and quick, friendly, and professional service.