Region:North America
Author(s):Dev
Product Code:KRAB3115
Pages:95
Published On:October 2025
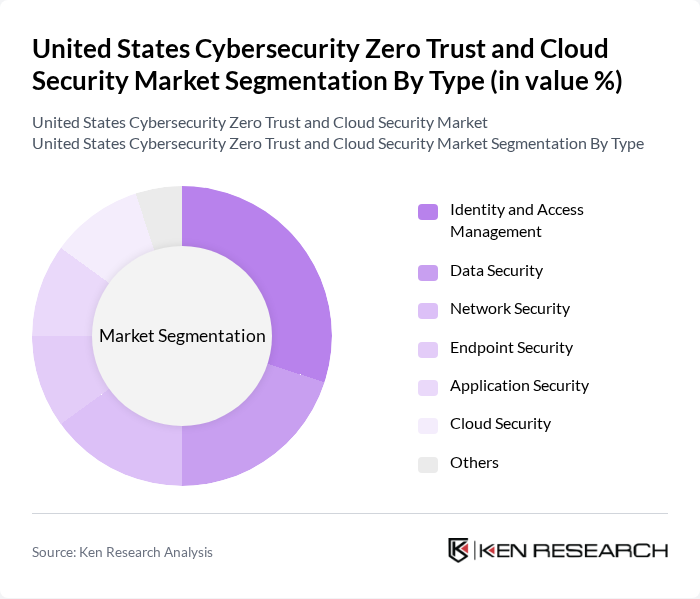
By Type:The market is segmented into various types, including Identity and Access Management, Data Security, Network Security, Endpoint Security, Application Security, Cloud Security, and Others. Among these, Identity and Access Management is currently the leading sub-segment due to the increasing need for secure user authentication and access control mechanisms in organizations.
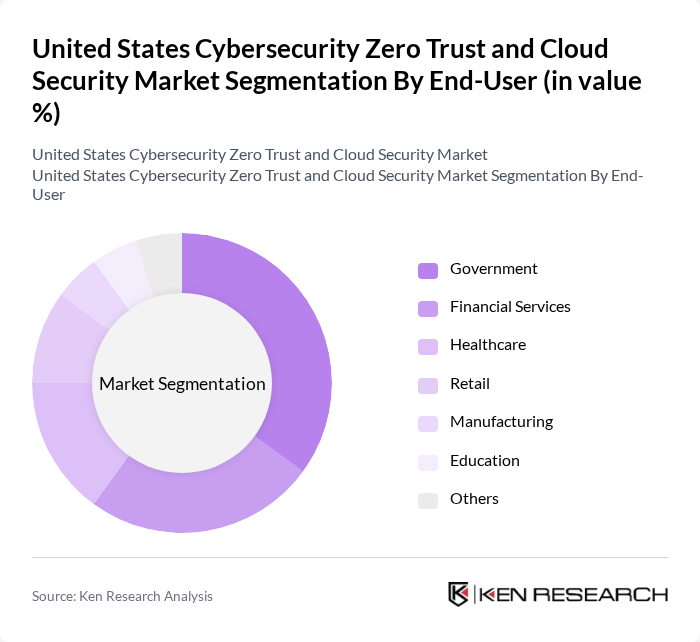
By End-User:The market is segmented by end-users, including Government, Financial Services, Healthcare, Retail, Manufacturing, Education, and Others. The Government sector is the dominant end-user, driven by the need for enhanced security measures to protect sensitive data and comply with federal regulations.
The United States Cybersecurity Zero Trust and Cloud Security Market is characterized by a dynamic mix of regional and international players. Leading participants such as Palo Alto Networks, Zscaler, Okta, Cisco Systems, Fortinet, CrowdStrike, Check Point Software Technologies, Microsoft, IBM, McAfee, Trend Micro, FireEye, RSA Security, Splunk, ServiceNow contribute to innovation, geographic expansion, and service delivery in this space.
As the cybersecurity landscape continues to evolve, organizations will increasingly prioritize Zero Trust architectures and cloud security solutions to combat rising threats. The integration of artificial intelligence and machine learning into security protocols will enhance threat detection and response capabilities. Additionally, the growing emphasis on regulatory compliance will drive further investments in security solutions. By the future, the market is expected to see a significant shift towards automated security measures, enabling organizations to respond more effectively to emerging cyber threats.
| Segment | Sub-Segments |
|---|---|
| By Type | Identity and Access Management Data Security Network Security Endpoint Security Application Security Cloud Security Others |
| By End-User | Government Financial Services Healthcare Retail Manufacturing Education Others |
| By Deployment Model | On-Premises Cloud-Based Hybrid |
| By Component | Solutions Services |
| By Sales Channel | Direct Sales Distributors Online Sales |
| By Industry Vertical | IT and Telecom Energy and Utilities Transportation and Logistics |
| By Pricing Model | Subscription-Based Pay-As-You-Go One-Time License Fee |
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Services Cybersecurity | 100 | Chief Information Security Officers, IT Security Managers |
| Healthcare Cloud Security | 80 | Healthcare IT Directors, Compliance Officers |
| Government Cybersecurity Initiatives | 70 | Government IT Managers, Cybersecurity Policy Makers |
| Retail Sector Zero Trust Adoption | 60 | IT Security Analysts, Operations Managers |
| Manufacturing Cloud Security Solutions | 90 | Manufacturing IT Directors, Risk Management Officers |
The United States Cybersecurity Zero Trust and Cloud Security Market is valued at approximately USD 45 billion, reflecting a significant increase driven by rising cyber threats, regulatory compliance needs, and the shift towards remote work.