About the Report
Base Year 2024Egypt Cybersecurity and Threat Intelligence Market Overview
- The Egypt Cybersecurity and Threat Intelligence Market is valued at USD 1.2 billion, based on a five-year historical analysis. This growth is primarily driven by the increasing frequency of cyber threats, the rise in digital transformation initiatives, and the growing awareness of cybersecurity among businesses and government entities. The demand for robust cybersecurity solutions has surged as organizations seek to protect sensitive data and maintain operational integrity.
- Cairo, Alexandria, and Giza are the dominant cities in the Egypt Cybersecurity and Threat Intelligence Market. Cairo, as the capital, hosts numerous government agencies and multinational corporations, making it a hub for cybersecurity investments. Alexandria, with its strategic port, is vital for logistics and trade, while Giza's proximity to Cairo enhances its role in the tech ecosystem, fostering innovation and collaboration in cybersecurity.
- In 2023, the Egyptian government implemented the Cybersecurity Law, which mandates that all organizations, both public and private, establish comprehensive cybersecurity frameworks. This regulation aims to enhance national security by ensuring that critical infrastructure and sensitive data are adequately protected against cyber threats, thereby promoting a safer digital environment for all stakeholders.
Egypt Cybersecurity and Threat Intelligence Market Segmentation
By Type:
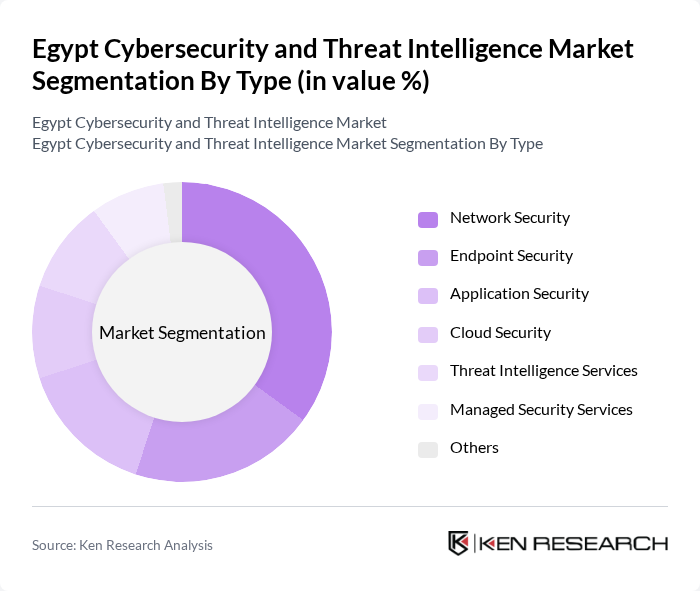
The market is segmented into various types, including Network Security, Endpoint Security, Application Security, Cloud Security, Threat Intelligence Services, Managed Security Services, and Others. Among these, Network Security is the leading sub-segment, driven by the increasing need to protect networks from unauthorized access and cyber threats. Organizations are investing heavily in firewalls, intrusion detection systems, and other network security solutions to safeguard their data and maintain business continuity. The growing trend of remote work has further amplified the demand for robust network security solutions, making it a critical focus area for businesses.
By End-User:
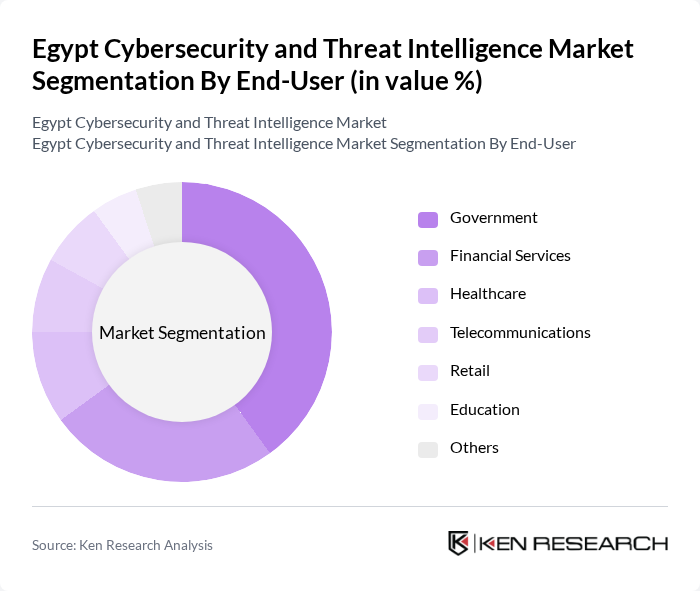
The end-user segmentation includes Government, Financial Services, Healthcare, Telecommunications, Retail, Education, and Others. The Government sector is the dominant end-user, as it invests significantly in cybersecurity to protect national security and critical infrastructure. The increasing number of cyberattacks targeting government agencies has led to heightened awareness and investment in cybersecurity measures. Additionally, the financial services sector is also a major contributor, driven by the need to protect sensitive financial data and comply with regulatory requirements.
Egypt Cybersecurity and Threat Intelligence Market Competitive Landscape
The Egypt Cybersecurity and Threat Intelligence Market is characterized by a dynamic mix of regional and international players. Leading participants such as IBM Security, Cisco Systems, Palo Alto Networks, Fortinet, Check Point Software Technologies, McAfee, Trend Micro, FireEye, CrowdStrike, RSA Security, CyberArk Software, Splunk, Darktrace, Proofpoint, Zscaler contribute to innovation, geographic expansion, and service delivery in this space.
Egypt Cybersecurity and Threat Intelligence Market Industry Analysis
Growth Drivers
- Increasing Cyber Threats:The Egyptian cybersecurity landscape is increasingly challenged by cyber threats, with reported incidents rising to over 1,200 in the future, a significant increase from 800 in the previous year. This surge is driven by the growing digitalization of businesses and government services, which has expanded the attack surface for cybercriminals. The World Bank estimates that Egypt's digital economy could reach $30 billion in the future, further intensifying the need for robust cybersecurity measures to protect sensitive data and infrastructure.
- Government Initiatives for Cybersecurity:The Egyptian government has prioritized cybersecurity, launching the National Cybersecurity Strategy in the previous year, which allocates approximately EGP 1.5 billion (around $48 million) for cybersecurity initiatives. This strategy aims to enhance national security and protect critical infrastructure. Additionally, the government is collaborating with international organizations to improve cybersecurity frameworks, which is expected to bolster the market significantly as public sector investments increase in the future.
- Rising Digital Transformation:Egypt's digital transformation is accelerating, with the digital economy projected to contribute 7% to the GDP in the future, up from 4% in the previous year. This transformation includes the adoption of e-commerce, online banking, and digital government services, which necessitate advanced cybersecurity solutions. As businesses increasingly rely on digital platforms, the demand for cybersecurity services is expected to grow, driving market expansion and innovation in security technologies.
Market Challenges
- Lack of Skilled Workforce:The cybersecurity sector in Egypt faces a significant skills gap, with an estimated shortage of 30,000 cybersecurity professionals as of the future. This shortage hampers the ability of organizations to implement effective security measures and respond to incidents promptly. The Egyptian government and educational institutions are working to address this issue, but the current lack of qualified personnel remains a critical challenge for the market's growth.
- High Implementation Costs:The costs associated with implementing comprehensive cybersecurity solutions can be prohibitive for many organizations, particularly small and medium-sized enterprises (SMEs). Initial investments in technology, training, and ongoing maintenance can exceed EGP 500,000 (approximately $16,000) for basic security setups. This financial barrier limits the adoption of necessary cybersecurity measures, leaving many businesses vulnerable to cyber threats and hindering overall market growth.
Egypt Cybersecurity and Threat Intelligence Market Future Outlook
The future of Egypt's cybersecurity and threat intelligence market appears promising, driven by increasing government support and a growing awareness of cyber risks among businesses. As digital transformation accelerates, organizations will prioritize investments in advanced security solutions, particularly in AI and machine learning technologies. Additionally, the collaboration between local firms and global cybersecurity leaders is expected to enhance capabilities and foster innovation, positioning Egypt as a regional cybersecurity hub in the future.
Market Opportunities
- Expansion of Cloud Security Solutions:With cloud adoption projected to grow by 25% in the future, there is a significant opportunity for cybersecurity firms to develop tailored cloud security solutions. This growth is driven by businesses seeking to protect sensitive data stored in the cloud, creating a demand for innovative security services that can address specific vulnerabilities associated with cloud environments.
- Increased Investment in Threat Intelligence:As organizations recognize the importance of proactive threat detection, investments in threat intelligence solutions are expected to rise. The market for threat intelligence services is anticipated to grow by EGP 200 million (approximately $6.4 million) in the future, as businesses seek to enhance their security posture and respond effectively to emerging threats in real-time.
Scope of the Report
| Segment | Sub-Segments |
|---|---|
| By Type | Network Security Endpoint Security Application Security Cloud Security Threat Intelligence Services Managed Security Services Others |
| By End-User | Government Financial Services Healthcare Telecommunications Retail Education Others |
| By Industry Vertical | Banking and Financial Services Energy and Utilities Manufacturing Transportation and Logistics Government and Defense Others |
| By Deployment Mode | On-Premises Cloud-Based Hybrid |
| By Service Type | Consulting Services Implementation Services Support and Maintenance Services |
| By Region | Cairo Alexandria Giza Others |
| By Pricing Model | Subscription-Based Pay-Per-Use One-Time License Fee |
Key Target Audience
Investors and Venture Capitalist Firms
Government and Regulatory Bodies (e.g., National Telecommunications Regulatory Authority, Ministry of Communications and Information Technology)
Cybersecurity Solution Providers
Telecommunications Companies
Financial Institutions
Critical Infrastructure Operators
Insurance Companies
Large Enterprises and Corporations
Players Mentioned in the Report:
IBM Security
Cisco Systems
Palo Alto Networks
Fortinet
Check Point Software Technologies
McAfee
Trend Micro
FireEye
CrowdStrike
RSA Security
CyberArk Software
Splunk
Darktrace
Proofpoint
Zscaler
Table of Contents
Market Assessment Phase
1. Executive Summary and Approach
2. Egypt Cybersecurity and Threat Intelligence Market Overview
2.1 Key Insights and Strategic Recommendations
2.2 Egypt Cybersecurity and Threat Intelligence Market Overview
2.3 Definition and Scope
2.4 Evolution of Market Ecosystem
2.5 Timeline of Key Regulatory Milestones
2.6 Value Chain & Stakeholder Mapping
2.7 Business Cycle Analysis
2.8 Policy & Incentive Landscape
3. Egypt Cybersecurity and Threat Intelligence Market Analysis
3.1 Growth Drivers
3.1.1 Increasing Cyber Threats
3.1.2 Government Initiatives for Cybersecurity
3.1.3 Rising Digital Transformation
3.1.4 Growing Awareness of Cybersecurity
3.2 Market Challenges
3.2.1 Lack of Skilled Workforce
3.2.2 High Implementation Costs
3.2.3 Evolving Cyber Threat Landscape
3.2.4 Regulatory Compliance Issues
3.3 Market Opportunities
3.3.1 Expansion of Cloud Security Solutions
3.3.2 Increased Investment in Threat Intelligence
3.3.3 Development of AI-Driven Security Solutions
3.3.4 Partnerships with Global Cybersecurity Firms
3.4 Market Trends
3.4.1 Adoption of Zero Trust Security Models
3.4.2 Integration of AI and Machine Learning
3.4.3 Growth of Managed Security Services
3.4.4 Focus on Data Privacy Regulations
3.5 Government Regulation
3.5.1 Cybersecurity Law Implementation
3.5.2 Data Protection Regulations
3.5.3 National Cybersecurity Strategy
3.5.4 Compliance with International Standards
4. SWOT Analysis
5. Stakeholder Analysis
6. Porter's Five Forces Analysis
7. Egypt Cybersecurity and Threat Intelligence Market Market Size, 2019-2024
7.1 By Value
7.2 By Volume
7.3 By Average Selling Price
8. Egypt Cybersecurity and Threat Intelligence Market Segmentation
8.1 By Type
8.1.1 Network Security
8.1.2 Endpoint Security
8.1.3 Application Security
8.1.4 Cloud Security
8.1.5 Threat Intelligence Services
8.1.6 Managed Security Services
8.1.7 Others
8.2 By End-User
8.2.1 Government
8.2.2 Financial Services
8.2.3 Healthcare
8.2.4 Telecommunications
8.2.5 Retail
8.2.6 Education
8.2.7 Others
8.3 By Industry Vertical
8.3.1 Banking and Financial Services
8.3.2 Energy and Utilities
8.3.3 Manufacturing
8.3.4 Transportation and Logistics
8.3.5 Government and Defense
8.3.6 Others
8.4 By Deployment Mode
8.4.1 On-Premises
8.4.2 Cloud-Based
8.4.3 Hybrid
8.5 By Service Type
8.5.1 Consulting Services
8.5.2 Implementation Services
8.5.3 Support and Maintenance Services
8.6 By Region
8.6.1 Cairo
8.6.2 Alexandria
8.6.3 Giza
8.6.4 Others
8.7 By Pricing Model
8.7.1 Subscription-Based
8.7.2 Pay-Per-Use
8.7.3 One-Time License Fee
9. Egypt Cybersecurity and Threat Intelligence Market Competitive Analysis
9.1 Market Share of Key Players
9.2 Cross Comparison of Key Players
9.2.1 Company Name
9.2.2 Group Size (Large, Medium, or Small as per industry convention)
9.2.3 Revenue Growth Rate
9.2.4 Customer Acquisition Cost
9.2.5 Customer Retention Rate
9.2.6 Market Penetration Rate
9.2.7 Pricing Strategy
9.2.8 Average Deal Size
9.2.9 Service Level Agreement Compliance
9.2.10 Brand Recognition Score
9.3 SWOT Analysis of Top Players
9.4 Pricing Analysis
9.5 Detailed Profile of Major Companies
9.5.1 IBM Security
9.5.2 Cisco Systems
9.5.3 Palo Alto Networks
9.5.4 Fortinet
9.5.5 Check Point Software Technologies
9.5.6 McAfee
9.5.7 Trend Micro
9.5.8 FireEye
9.5.9 CrowdStrike
9.5.10 RSA Security
9.5.11 CyberArk Software
9.5.12 Splunk
9.5.13 Darktrace
9.5.14 Proofpoint
9.5.15 Zscaler
10. Egypt Cybersecurity and Threat Intelligence Market End-User Analysis
10.1 Procurement Behavior of Key Ministries
10.1.1 Ministry of Communications and Information Technology
10.1.2 Ministry of Interior
10.1.3 Ministry of Defense
10.1.4 Ministry of Finance
10.2 Corporate Spend on Infrastructure & Energy
10.2.1 IT Infrastructure Investments
10.2.2 Cybersecurity Training Budgets
10.2.3 Software Licensing Costs
10.3 Pain Point Analysis by End-User Category
10.3.1 Data Breaches
10.3.2 Compliance Challenges
10.3.3 Resource Limitations
10.4 User Readiness for Adoption
10.4.1 Awareness Levels
10.4.2 Training Needs
10.4.3 Technology Adoption Rates
10.5 Post-Deployment ROI and Use Case Expansion
10.5.1 Cost Savings from Threat Prevention
10.5.2 Increased Operational Efficiency
10.5.3 Enhanced Customer Trust
11. Egypt Cybersecurity and Threat Intelligence Market Future Size, 2025-2030
11.1 By Value
11.2 By Volume
11.3 By Average Selling Price
Go-To-Market Strategy Phase
1. Whitespace Analysis + Business Model Canvas
1.1 Market Gaps Identification
1.2 Value Proposition Development
1.3 Revenue Streams Analysis
1.4 Key Partnerships Exploration
1.5 Customer Segmentation
1.6 Cost Structure Analysis
1.7 Competitive Advantage Assessment
2. Marketing and Positioning Recommendations
2.1 Branding Strategies
2.2 Product USPs
2.3 Target Audience Identification
2.4 Communication Channels
2.5 Marketing Budget Allocation
3. Distribution Plan
3.1 Urban Retail Strategies
3.2 Rural NGO Tie-Ups
3.3 Online Distribution Channels
3.4 Direct Sales Approaches
4. Channel & Pricing Gaps
4.1 Underserved Routes
4.2 Pricing Bands Analysis
4.3 Competitor Pricing Comparison
5. Unmet Demand & Latent Needs
5.1 Category Gaps
5.2 Consumer Segments
5.3 Emerging Trends
6. Customer Relationship
6.1 Loyalty Programs
6.2 After-Sales Service
6.3 Customer Feedback Mechanisms
7. Value Proposition
7.1 Sustainability Initiatives
7.2 Integrated Supply Chains
7.3 Unique Selling Points
8. Key Activities
8.1 Regulatory Compliance
8.2 Branding Efforts
8.3 Distribution Setup
9. Entry Strategy Evaluation
9.1 Domestic Market Entry Strategy
9.1.1 Product Mix
9.1.2 Pricing Band
9.1.3 Packaging
9.2 Export Entry Strategy
9.2.1 Target Countries
9.2.2 Compliance Roadmap
10. Entry Mode Assessment
10.1 Joint Ventures
10.2 Greenfield Investments
10.3 Mergers & Acquisitions
10.4 Distributor Model
11. Capital and Timeline Estimation
11.1 Capital Requirements
11.2 Timelines
12. Control vs Risk Trade-Off
12.1 Ownership vs Partnerships
13. Profitability Outlook
13.1 Breakeven Analysis
13.2 Long-Term Sustainability
14. Potential Partner List
14.1 Distributors
14.2 Joint Ventures
14.3 Acquisition Targets
15. Execution Roadmap
15.1 Phased Plan for Market Entry
15.1.1 Market Setup
15.1.2 Market Entry
15.1.3 Growth Acceleration
15.1.4 Scale & Stabilize
15.2 Key Activities and Milestones
15.2.1 Milestone Planning
15.2.2 Activity Scheduling
Research Methodology
Phase 1: Approach1
Desk Research
- Analysis of government publications and cybersecurity frameworks from the Egyptian government
- Review of industry reports and white papers from cybersecurity associations and think tanks
- Examination of market trends and statistics from reputable cybersecurity research firms
Primary Research
- Interviews with cybersecurity experts and analysts in Egypt's tech ecosystem
- Surveys targeting IT managers and security officers in various sectors
- Focus groups with stakeholders from government and private sectors on threat intelligence practices
Validation & Triangulation
- Cross-validation of findings through multiple data sources, including academic journals and industry publications
- Triangulation of qualitative insights from interviews with quantitative data from surveys
- Sanity checks conducted through expert panel reviews and feedback sessions
Phase 2: Market Size Estimation1
Top-down Assessment
- Estimation of the overall cybersecurity market size based on national IT spending reports
- Segmentation of the market by industry verticals such as finance, healthcare, and government
- Incorporation of growth rates from regional cybersecurity initiatives and investments
Bottom-up Modeling
- Data collection from leading cybersecurity firms on service offerings and pricing models
- Estimation of market penetration rates based on firm-level sales data
- Volume x pricing analysis for various cybersecurity services and products
Forecasting & Scenario Analysis
- Multi-factor regression analysis incorporating economic indicators and cyber threat trends
- Scenario modeling based on potential regulatory changes and technological advancements
- Development of baseline, optimistic, and pessimistic forecasts through 2030
Phase 3: CATI Sample Composition1
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Sector Cybersecurity | 100 | IT Security Managers, Risk Assessment Officers |
| Healthcare Data Protection | 80 | Compliance Officers, IT Directors |
| Government Cyber Defense Strategies | 70 | Policy Makers, Cybersecurity Analysts |
| SME Cybersecurity Solutions | 90 | Business Owners, IT Consultants |
| Threat Intelligence Sharing Practices | 60 | Security Operations Center (SOC) Managers, Threat Analysts |
Frequently Asked Questions
What is the current value of the Egypt Cybersecurity and Threat Intelligence Market?
The Egypt Cybersecurity and Threat Intelligence Market is valued at approximately USD 1.2 billion, reflecting significant growth driven by increasing cyber threats, digital transformation initiatives, and heightened awareness of cybersecurity among businesses and government entities.