About the Report
Base Year 2024GCC Data Centric Security Market Overview
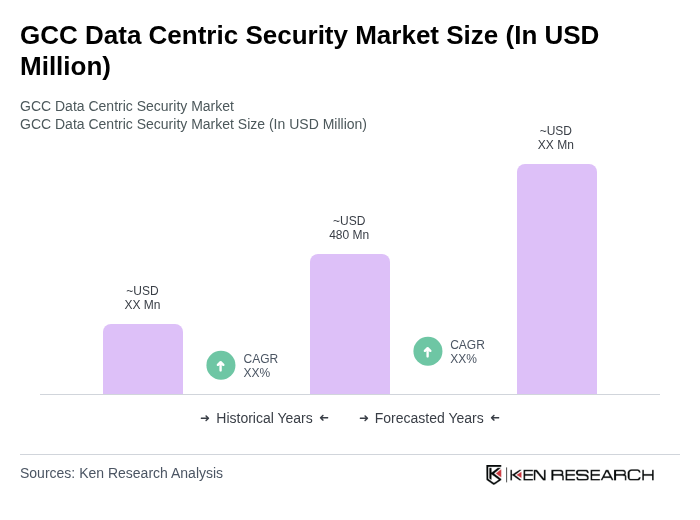
- The GCC Data Centric Security Market is valued at USD 480 million, based on a five-year historical analysis and normalization from global and regional benchmarks. This growth is primarily driven by the increasing need for data protection due to rising cyber threats, expanding regulatory compliance requirements, and the rapid adoption of digital transformation initiatives across sectors. Organizations are investing significantly in data-centric security solutions to safeguard sensitive information, address privacy concerns, and maintain customer trust.
- The United Arab Emirates and Saudi Arabia dominate the market due to their advanced technological infrastructure, high internet penetration rates, and proactive government initiatives aimed at enhancing cybersecurity. These countries have established themselves as regional hubs for technology and innovation, attracting investments and fostering a competitive environment for data-centric security solutions.
- The UAE Federal Decree-Law No. 45 of 2021 on the Protection of Personal Data, issued by the United Arab Emirates Cabinet, mandates organizations to adopt stringent measures for data security and privacy. This regulation enhances consumer trust and ensures compliance with international standards, thereby driving the demand for data-centric security solutions across various industries. Key operational requirements include data subject rights, breach notification obligations, and mandatory data protection impact assessments.
GCC Data Centric Security Market Segmentation
By Type:The market is segmented into various types of data-centric security solutions, including Data Encryption, Data Masking, Tokenization, Data Loss Prevention, and Others. Each of these sub-segments plays a crucial role in addressing specific security needs of organizations.
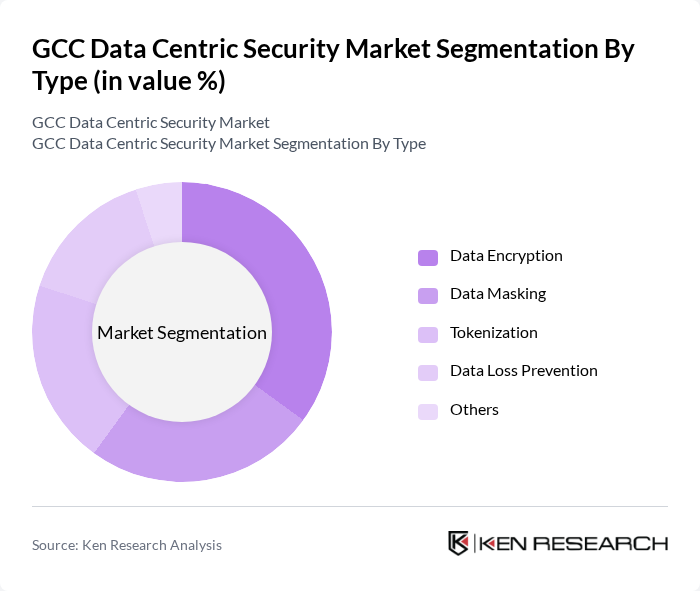
The Data Encryption sub-segment is currently dominating the market due to the increasing need for organizations to protect sensitive data from unauthorized access and breaches. With the rise in cyber threats and stringent regulations, businesses are prioritizing encryption technologies to secure their data both at rest and in transit. This trend is further fueled by the growing adoption of cloud services, where encryption is essential for safeguarding data stored in the cloud.
By End-User:The market is segmented by end-users, including Banking and Financial Services, Healthcare, Retail, Government, and Others. Each sector has unique security requirements that drive the adoption of data-centric security solutions.
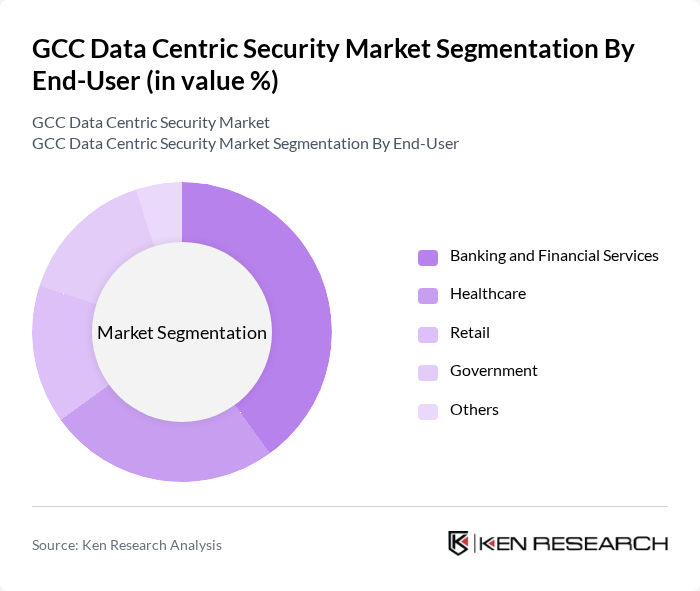
The Banking and Financial Services sector leads the market due to the critical need for protecting sensitive financial data and complying with stringent regulations. Financial institutions are increasingly investing in data-centric security solutions to mitigate risks associated with data breaches and fraud, ensuring the safety of customer information and maintaining regulatory compliance.
GCC Data Centric Security Market Competitive Landscape
The GCC Data Centric Security Market is characterized by a dynamic mix of regional and international players. Leading participants such as IBM, McAfee, Broadcom (Symantec), RSA Security, Thales Group, Digital Guardian, Forcepoint, Trend Micro, Check Point Software Technologies, Palo Alto Networks, Fortinet, CyberArk, Varonis, Zscaler, Proofpoint, DarkMatter, SecureData, CyberKnight, Gulf Business Machines (GBM), Alcatel-Lucent Enterprise contribute to innovation, geographic expansion, and service delivery in this space.
GCC Data Centric Security Market Industry Analysis
Growth Drivers
- Increasing Cybersecurity Threats:The GCC region has witnessed a significant rise in cybersecurity incidents, with reported breaches increasing by 30% in future. According to the International Telecommunication Union, the cost of cybercrime in the Middle East is projected to reach $1.6 billion in future. This alarming trend drives organizations to invest heavily in data-centric security solutions to protect sensitive information and maintain operational integrity, thereby fueling market growth.
- Regulatory Compliance Requirements:Governments in the GCC are implementing stringent data protection regulations, such as the UAE's Data Protection Law, which came into effect in future. Compliance with these regulations is mandatory for businesses, leading to an estimated increase in spending on data security solutions by 25% in future. This regulatory landscape compels organizations to adopt robust data-centric security measures to avoid hefty fines and reputational damage, thus driving market expansion.
- Rising Data Privacy Concerns:With the growing awareness of data privacy among consumers, organizations in the GCC are prioritizing data protection. A survey by PwC indicates that 70% of consumers in the region are concerned about how their data is used. This heightened concern is prompting businesses to invest in advanced data-centric security solutions, leading to an estimated market growth of $350 million in future as companies strive to enhance their data privacy practices and build consumer trust.
Market Challenges
- High Implementation Costs:The initial investment required for implementing comprehensive data-centric security solutions can be prohibitive for many organizations. A report from Gartner indicates that the average cost of deploying a robust cybersecurity framework in the GCC can exceed $1.2 million, particularly for small to medium-sized enterprises. This financial barrier limits the adoption of necessary security measures, posing a significant challenge to market growth.
- Lack of Skilled Workforce:The GCC faces a critical shortage of cybersecurity professionals, with an estimated 3.5 million unfilled positions globally, according to Cybersecurity Ventures. In the GCC, the skills gap is particularly pronounced, with only 20% of organizations reporting adequate cybersecurity expertise. This lack of skilled personnel hampers the effective implementation and management of data-centric security solutions, creating a substantial challenge for the market.
GCC Data Centric Security Market Future Outlook
The GCC Data Centric Security Market is poised for significant transformation as organizations increasingly adopt advanced technologies to combat evolving cyber threats. The shift towards zero trust security models and the integration of AI-driven solutions are expected to redefine security strategies. Additionally, the expansion of digital transformation initiatives across various sectors will further drive demand for robust data protection measures, ensuring that businesses remain resilient against potential data breaches and compliance challenges in the coming years.
Market Opportunities
- Growth in IoT Devices:The proliferation of IoT devices in the GCC, projected to reach 1.6 billion in future, presents a significant opportunity for data-centric security solutions. As these devices become integral to business operations, the demand for enhanced security measures to protect sensitive data transmitted through IoT networks will surge, creating a lucrative market segment.
- Development of AI-Driven Security Solutions:The increasing sophistication of cyber threats necessitates the development of AI-driven security solutions. The GCC is expected to see a 45% rise in investment in AI-based cybersecurity technologies in future. This trend offers a substantial opportunity for companies to innovate and provide advanced security solutions that can proactively address emerging threats in real-time.
Scope of the Report
| Segment | Sub-Segments |
|---|---|
| By Type | Data Encryption Data Masking Tokenization Data Loss Prevention Others |
| By End-User | Banking and Financial Services Healthcare Retail Government Others |
| By Deployment Model | On-Premises Cloud-Based Hybrid Others |
| By Industry Vertical | Telecommunications Manufacturing Education Energy and Utilities Others |
| By Region | United Arab Emirates Saudi Arabia Qatar Kuwait Others |
| By Security Type | Network Security Endpoint Security Application Security Cloud Security Others |
| By Service Type | Consulting Services Implementation Services Managed Services Training and Support Services Others |
Key Target Audience
Investors and Venture Capitalist Firms
Government and Regulatory Bodies (e.g., Ministry of Interior, National Cybersecurity Authority)
Data Security Solution Providers
Telecommunications Companies
Cloud Service Providers
Financial Institutions and Banks
Healthcare Organizations
Energy and Utility Companies
Players Mentioned in the Report:
IBM
McAfee
Broadcom (Symantec)
RSA Security
Thales Group
Digital Guardian
Forcepoint
Trend Micro
Check Point Software Technologies
Palo Alto Networks
Fortinet
CyberArk
Varonis
Zscaler
Proofpoint
DarkMatter
SecureData
CyberKnight
Gulf Business Machines (GBM)
Alcatel-Lucent Enterprise
Table of Contents
Market Assessment Phase
1. Executive Summary and Approach
2. GCC Data Centric Security Market Overview
2.1 Key Insights and Strategic Recommendations
2.2 GCC Data Centric Security Market Overview
2.3 Definition and Scope
2.4 Evolution of Market Ecosystem
2.5 Timeline of Key Regulatory Milestones
2.6 Value Chain & Stakeholder Mapping
2.7 Business Cycle Analysis
2.8 Policy & Incentive Landscape
3. GCC Data Centric Security Market Analysis
3.1 Growth Drivers
3.1.1 Increasing Cybersecurity Threats
3.1.2 Regulatory Compliance Requirements
3.1.3 Rising Data Privacy Concerns
3.1.4 Adoption of Cloud Technologies
3.2 Market Challenges
3.2.1 High Implementation Costs
3.2.2 Lack of Skilled Workforce
3.2.3 Rapidly Evolving Threat Landscape
3.2.4 Integration with Legacy Systems
3.3 Market Opportunities
3.3.1 Growth in IoT Devices
3.3.2 Expansion of Digital Transformation Initiatives
3.3.3 Increased Investment in Cybersecurity Solutions
3.3.4 Development of AI-Driven Security Solutions
3.4 Market Trends
3.4.1 Shift Towards Zero Trust Security Models
3.4.2 Increased Focus on Data Encryption
3.4.3 Rise of Managed Security Service Providers (MSSPs)
3.4.4 Growing Importance of Data Governance
3.5 Government Regulation
3.5.1 Data Protection Laws
3.5.2 Cybersecurity Frameworks
3.5.3 Compliance Mandates for Financial Institutions
3.5.4 National Cybersecurity Strategies
4. SWOT Analysis
5. Stakeholder Analysis
6. Porter's Five Forces Analysis
7. GCC Data Centric Security Market Market Size, 2019-2024
7.1 By Value
7.2 By Volume
7.3 By Average Selling Price
8. GCC Data Centric Security Market Segmentation
8.1 By Type
8.1.1 Data Encryption
8.1.2 Data Masking
8.1.3 Tokenization
8.1.4 Data Loss Prevention
8.1.5 Others
8.2 By End-User
8.2.1 Banking and Financial Services
8.2.2 Healthcare
8.2.3 Retail
8.2.4 Government
8.2.5 Others
8.3 By Deployment Model
8.3.1 On-Premises
8.3.2 Cloud-Based
8.3.3 Hybrid
8.3.4 Others
8.4 By Industry Vertical
8.4.1 Telecommunications
8.4.2 Manufacturing
8.4.3 Education
8.4.4 Energy and Utilities
8.4.5 Others
8.5 By Region
8.5.1 United Arab Emirates
8.5.2 Saudi Arabia
8.5.3 Qatar
8.5.4 Kuwait
8.5.5 Others
8.6 By Security Type
8.6.1 Network Security
8.6.2 Endpoint Security
8.6.3 Application Security
8.6.4 Cloud Security
8.6.5 Others
8.7 By Service Type
8.7.1 Consulting Services
8.7.2 Implementation Services
8.7.3 Managed Services
8.7.4 Training and Support Services
8.7.5 Others
9. GCC Data Centric Security Market Competitive Analysis
9.1 Market Share of Key Players
9.2 Cross Comparison of Key Players
9.2.1 Company Name
9.2.2 Group Size (Large, Medium, or Small as per industry convention)
9.2.3 Revenue Growth Rate (GCC region)
9.2.4 Customer Retention Rate (GCC region)
9.2.5 Market Penetration Rate (GCC region)
9.2.6 Pricing Strategy (GCC-specific)
9.2.7 Product Innovation Rate (GCC-focused launches)
9.2.8 Operational Efficiency (GCC delivery and support)
9.2.9 Customer Satisfaction Score (GCC client feedback)
9.2.10 Brand Recognition (GCC market awareness)
9.3 SWOT Analysis of Top Players
9.4 Pricing Analysis
9.5 Detailed Profile of Major Companies
9.5.1 IBM
9.5.2 McAfee
9.5.3 Broadcom (Symantec)
9.5.4 RSA Security
9.5.5 Thales Group
9.5.6 Digital Guardian
9.5.7 Forcepoint
9.5.8 Trend Micro
9.5.9 Check Point Software Technologies
9.5.10 Palo Alto Networks
9.5.11 Fortinet
9.5.12 CyberArk
9.5.13 Varonis
9.5.14 Zscaler
9.5.15 Proofpoint
9.5.16 DarkMatter
9.5.17 SecureData
9.5.18 CyberKnight
9.5.19 Gulf Business Machines (GBM)
9.5.20 Alcatel-Lucent Enterprise
10. GCC Data Centric Security Market End-User Analysis
10.1 Procurement Behavior of Key Ministries
10.1.1 Budget Allocation Trends
10.1.2 Decision-Making Processes
10.1.3 Preferred Vendors
10.1.4 Compliance Requirements
10.2 Corporate Spend on Infrastructure & Energy
10.2.1 Investment Trends
10.2.2 Spending Priorities
10.2.3 Budget Cycles
10.2.4 Cost-Benefit Analysis
10.3 Pain Point Analysis by End-User Category
10.3.1 Security Gaps
10.3.2 Compliance Challenges
10.3.3 Resource Constraints
10.3.4 Technology Integration Issues
10.4 User Readiness for Adoption
10.4.1 Awareness Levels
10.4.2 Training Needs
10.4.3 Infrastructure Readiness
10.4.4 Change Management Strategies
10.5 Post-Deployment ROI and Use Case Expansion
10.5.1 Performance Metrics
10.5.2 User Feedback
10.5.3 Scalability Potential
10.5.4 Future Investment Plans
11. GCC Data Centric Security Market Future Size, 2025-2030
11.1 By Value
11.2 By Volume
11.3 By Average Selling Price
Go-To-Market Strategy Phase
1. Whitespace Analysis + Business Model Canvas
1.1 Market Gaps Identification
1.2 Value Proposition Development
1.3 Revenue Streams Analysis
1.4 Cost Structure Evaluation
1.5 Key Partnerships Exploration
1.6 Customer Segmentation
1.7 Competitive Advantage Assessment
2. Marketing and Positioning Recommendations
2.1 Branding Strategies
2.2 Product USPs
2.3 Target Audience Identification
2.4 Communication Channels
2.5 Marketing Budget Allocation
3. Distribution Plan
3.1 Urban Retail Strategies
3.2 Rural NGO Tie-Ups
3.3 Online Distribution Channels
3.4 Direct Sales Approaches
3.5 Partnership Opportunities
4. Channel & Pricing Gaps
4.1 Underserved Routes
4.2 Pricing Bands Analysis
4.3 Competitor Pricing Strategies
4.4 Customer Willingness to Pay
4.5 Value-Based Pricing Models
5. Unmet Demand & Latent Needs
5.1 Category Gaps
5.2 Consumer Segments Analysis
5.3 Emerging Trends Identification
5.4 Future Needs Forecasting
5.5 Product Development Opportunities
6. Customer Relationship
6.1 Loyalty Programs
6.2 After-Sales Service
6.3 Customer Engagement Strategies
6.4 Feedback Mechanisms
6.5 Relationship Management Tools
7. Value Proposition
7.1 Sustainability Initiatives
7.2 Integrated Supply Chains
7.3 Customer-Centric Solutions
7.4 Competitive Differentiation
7.5 Long-Term Value Creation
8. Key Activities
8.1 Regulatory Compliance
8.2 Branding Efforts
8.3 Distribution Setup
8.4 Training and Development
8.5 Performance Monitoring
9. Entry Strategy Evaluation
9.1 Domestic Market Entry Strategy
9.1.1 Product Mix
9.1.2 Pricing Band
9.1.3 Packaging Strategies
9.2 Export Entry Strategy
9.2.1 Target Countries
9.2.2 Compliance Roadmap
10. Entry Mode Assessment
10.1 Joint Ventures
10.2 Greenfield Investments
10.3 Mergers & Acquisitions
10.4 Distributor Model
10.5 Risk Assessment
11. Capital and Timeline Estimation
11.1 Capital Requirements
11.2 Timelines for Implementation
11.3 Financial Projections
11.4 Funding Sources
11.5 Budget Allocation
12. Control vs Risk Trade-Off
12.1 Ownership vs Partnerships
12.2 Risk Mitigation Strategies
12.3 Control Mechanisms
12.4 Partnership Evaluation
12.5 Long-Term Strategy Alignment
13. Profitability Outlook
13.1 Breakeven Analysis
13.2 Long-Term Sustainability
13.3 Profit Margin Projections
13.4 Revenue Growth Forecast
13.5 Cost Management Strategies
14. Potential Partner List
14.1 Distributors
14.2 Joint Ventures
14.3 Acquisition Targets
14.4 Strategic Alliances
14.5 Partnership Opportunities
15. Execution Roadmap
15.1 Phased Plan for Market Entry
15.1.1 Market Setup
15.1.2 Market Entry
15.1.3 Growth Acceleration
15.1.4 Scale & Stabilize
15.2 Key Activities and Milestones
15.2.1 Activity Planning
15.2.2 Milestone Tracking
15.2.3 Performance Evaluation
15.2.4 Adjustment Strategies
Research Methodology
Phase 1: Approach1
Desk Research
- Analysis of industry reports from leading market research firms focusing on data-centric security trends in the GCC region
- Review of white papers and publications from cybersecurity associations and governmental bodies
- Examination of market statistics and forecasts from reputable databases and industry journals
Primary Research
- Interviews with IT security managers and data protection officers in key GCC enterprises
- Surveys targeting decision-makers in sectors heavily reliant on data security, such as finance and healthcare
- Field interviews with cybersecurity consultants and technology vendors operating in the GCC market
Validation & Triangulation
- Cross-validation of findings through multiple data sources, including market reports and expert opinions
- Triangulation of qualitative insights from interviews with quantitative data from surveys
- Sanity checks conducted through expert panel reviews to ensure data accuracy and relevance
Phase 2: Market Size Estimation1
Top-down Assessment
- Estimation of the overall cybersecurity market size in the GCC, focusing on data-centric security solutions
- Segmentation of the market by industry verticals, including finance, healthcare, and government
- Incorporation of regional regulatory frameworks and their impact on data security investments
Bottom-up Modeling
- Collection of firm-level data from leading data-centric security solution providers in the GCC
- Estimation of market penetration rates based on current adoption trends in various sectors
- Calculation of revenue potential based on average deal sizes and frequency of purchases
Forecasting & Scenario Analysis
- Multi-factor regression analysis incorporating variables such as data breach incidents and regulatory changes
- Scenario modeling based on potential shifts in technology adoption and market dynamics
- Development of baseline, optimistic, and pessimistic forecasts through 2030
Phase 3: CATI Sample Composition1
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Services Data Security | 100 | IT Security Managers, Compliance Officers |
| Healthcare Data Protection | 70 | Data Protection Officers, IT Directors |
| Government Cybersecurity Initiatives | 60 | Cybersecurity Policy Makers, IT Administrators |
| Retail Sector Data Security Solutions | 50 | Operations Managers, IT Security Analysts |
| Telecommunications Data Privacy | 60 | Network Security Engineers, Compliance Managers |
Frequently Asked Questions
What is the current value of the GCC Data Centric Security Market?
The GCC Data Centric Security Market is valued at approximately USD 480 million, reflecting significant growth driven by increasing cyber threats, regulatory compliance needs, and the rapid adoption of digital transformation initiatives across various sectors.