About the Report
Base Year 2024South Africa Cybersecurity in Telecom Networks Market Overview
- The South Africa Cybersecurity in Telecom Networks Market is valued at USD 1.2 billion, based on a five-year historical analysis. This growth is primarily driven by the increasing frequency of cyber threats, the rise in mobile and internet penetration, and the growing need for regulatory compliance among telecom operators. The market is also supported by investments in advanced security technologies and services to protect sensitive data and infrastructure.
- Key cities dominating this market include Johannesburg, Cape Town, and Durban. Johannesburg, as the financial hub, has a high concentration of telecom operators and enterprises that require robust cybersecurity solutions. Cape Town is known for its tech innovation and startup ecosystem, while Durban's strategic port location makes it vital for logistics and communication, further driving the demand for cybersecurity in telecom networks.
- In 2023, the South African government implemented the Cybercrimes Act, which aims to combat cybercrime and enhance cybersecurity measures across various sectors, including telecommunications. This regulation mandates telecom operators to adopt stringent security protocols and report cyber incidents, thereby fostering a safer digital environment and promoting trust among consumers.
South Africa Cybersecurity in Telecom Networks Market Segmentation
By Type:The market is segmented into various types of cybersecurity solutions, including Network Security, Endpoint Security, Application Security, Cloud Security, Data Security, Identity and Access Management, and Others. Among these, Network Security is the most dominant segment due to the increasing need to protect network infrastructures from unauthorized access and cyber threats. The rise in sophisticated cyber-attacks has led organizations to prioritize network security solutions, ensuring the integrity and confidentiality of their data.

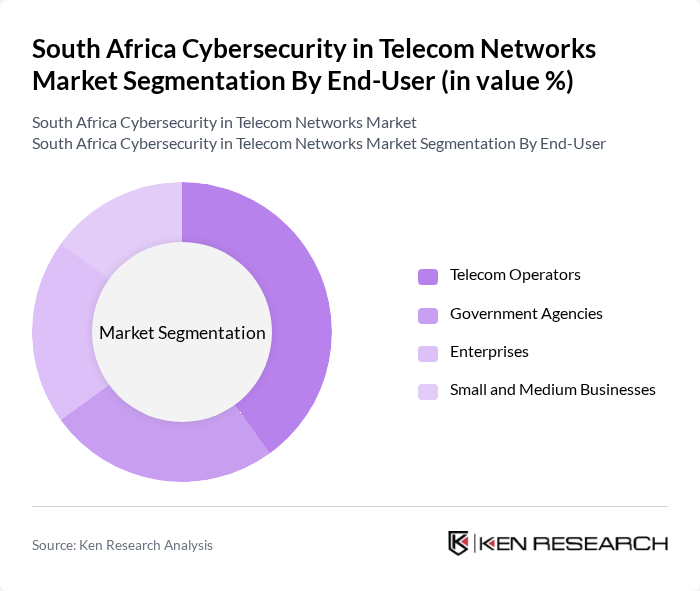
By End-User:The end-user segmentation includes Telecom Operators, Government Agencies, Enterprises, and Small and Medium Businesses (SMBs). Telecom Operators are the leading segment, driven by the necessity to secure vast networks and customer data against cyber threats. The increasing reliance on digital services and mobile connectivity has made telecom operators prioritize cybersecurity investments to maintain service integrity and customer trust.
South Africa Cybersecurity in Telecom Networks Market Competitive Landscape
The South Africa Cybersecurity in Telecom Networks Market is characterized by a dynamic mix of regional and international players. Leading participants such as Dimension Data, MTN Group, Vodacom Group, Telkom SA SOC Ltd, Darktrace, Check Point Software Technologies, Fortinet, Palo Alto Networks, IBM Security, Cisco Systems, Kaspersky Lab, McAfee, Trend Micro, Sophos, ESET contribute to innovation, geographic expansion, and service delivery in this space.
South Africa Cybersecurity in Telecom Networks Market Industry Analysis
Growth Drivers
- Increasing Cyber Threats:The South African telecom sector has witnessed a surge in cyber threats, with reported incidents increasing by 30% in the future, according to the South African Cyber Security Hub. This rise is attributed to the growing digitalization of services, which has expanded the attack surface for cybercriminals. The financial impact of these threats is significant, with estimated losses reaching R2.5 billion in the future, prompting telecom companies to invest heavily in cybersecurity measures to protect their networks and customer data.
- Regulatory Compliance Requirements:South Africa's regulatory landscape is becoming increasingly stringent, with the Protection of Personal Information Act (POPIA) mandating strict data protection measures. Compliance with POPIA is expected to cost telecom companies approximately R1.8 billion collectively in the future. Additionally, the Cybercrimes Act imposes penalties for data breaches, further driving the need for robust cybersecurity solutions. As a result, telecom providers are prioritizing investments in security technologies to ensure compliance and avoid hefty fines.
- Rising Demand for Secure Communication:The demand for secure communication channels is escalating, driven by the increasing reliance on digital platforms for business operations. In the future, the South African telecom market is projected to see a 25% increase in demand for secure communication solutions, as businesses seek to protect sensitive information. This trend is further supported by the growing adoption of remote work, which necessitates secure access to corporate networks, thereby boosting investments in cybersecurity infrastructure.
Market Challenges
- High Implementation Costs:The initial costs associated with implementing advanced cybersecurity solutions can be prohibitive for many telecom providers. In the future, the average expenditure on cybersecurity infrastructure is expected to exceed R1 billion per company, which can strain budgets, especially for smaller firms. This financial barrier often leads to delays in adopting necessary security measures, leaving networks vulnerable to attacks and increasing the risk of data breaches.
- Shortage of Skilled Professionals:The cybersecurity sector in South Africa faces a significant skills gap, with an estimated shortage of 40,000 cybersecurity professionals in the future. This deficit hampers the ability of telecom companies to effectively implement and manage security protocols. The lack of qualified personnel not only increases operational risks but also drives up costs as companies are forced to invest in training or outsourcing, further complicating their cybersecurity strategies.
South Africa Cybersecurity in Telecom Networks Market Future Outlook
The South African cybersecurity landscape in telecom networks is poised for transformative growth, driven by technological advancements and increasing regulatory pressures. As companies adopt AI and machine learning for threat detection, the efficiency of security measures will improve significantly. Furthermore, the expansion of 5G networks will necessitate enhanced security protocols, creating a robust demand for innovative solutions. Collaboration with international firms will also play a crucial role in elevating local capabilities, ensuring that South Africa remains competitive in the global cybersecurity arena.
Market Opportunities
- Growth in Cloud-Based Security Solutions:The shift towards cloud computing is creating substantial opportunities for cybersecurity providers. In the future, the market for cloud-based security solutions in South Africa is expected to grow by R1.5 billion, as businesses seek scalable and flexible security options. This trend is driven by the need for remote access and data protection, positioning cloud security as a critical component of telecom cybersecurity strategies.
- Expansion of 5G Networks:The rollout of 5G technology presents a unique opportunity for cybersecurity innovation. With an estimated R60 billion investment in 5G infrastructure by the future, telecom companies are focusing on securing these networks against potential threats. This expansion will drive demand for advanced security solutions tailored to the unique challenges posed by 5G, creating a lucrative market for cybersecurity firms.
Scope of the Report
| Segment | Sub-Segments |
|---|---|
| By Type | Network Security Endpoint Security Application Security Cloud Security Data Security Identity and Access Management Others |
| By End-User | Telecom Operators Government Agencies Enterprises Small and Medium Businesses |
| By Application | Fraud Detection Network Monitoring Incident Response Compliance Management |
| By Deployment Mode | On-Premises Cloud-Based |
| By Service Type | Consulting Services Managed Security Services Training and Support Services |
| By Region | Gauteng Western Cape KwaZulu-Natal Eastern Cape |
| By Pricing Model | Subscription-Based Pay-Per-Use One-Time License Fee |
Key Target Audience
Investors and Venture Capitalist Firms
Government and Regulatory Bodies (e.g., South African National Cybersecurity Hub, Independent Communications Authority of South Africa)
Telecom Network Operators
Cybersecurity Solution Providers
Telecom Equipment Manufacturers
Industry Associations (e.g., Telecommunications Industry Association of South Africa)
Telecom Infrastructure Providers
Financial Institutions and Banks
Players Mentioned in the Report:
Dimension Data
MTN Group
Vodacom Group
Telkom SA SOC Ltd
Darktrace
Check Point Software Technologies
Fortinet
Palo Alto Networks
IBM Security
Cisco Systems
Kaspersky Lab
McAfee
Trend Micro
Sophos
ESET
Table of Contents
Market Assessment Phase
1. Executive Summary and Approach
2. South Africa Cybersecurity in Telecom Networks Market Overview
2.1 Key Insights and Strategic Recommendations
2.2 South Africa Cybersecurity in Telecom Networks Market Overview
2.3 Definition and Scope
2.4 Evolution of Market Ecosystem
2.5 Timeline of Key Regulatory Milestones
2.6 Value Chain & Stakeholder Mapping
2.7 Business Cycle Analysis
2.8 Policy & Incentive Landscape
3. South Africa Cybersecurity in Telecom Networks Market Analysis
3.1 Growth Drivers
3.1.1 Increasing Cyber Threats
3.1.2 Regulatory Compliance Requirements
3.1.3 Rising Demand for Secure Communication
3.1.4 Technological Advancements in Security Solutions
3.2 Market Challenges
3.2.1 High Implementation Costs
3.2.2 Shortage of Skilled Professionals
3.2.3 Rapidly Evolving Threat Landscape
3.2.4 Integration Issues with Legacy Systems
3.3 Market Opportunities
3.3.1 Growth in Cloud-Based Security Solutions
3.3.2 Expansion of 5G Networks
3.3.3 Increased Investment in Cybersecurity Startups
3.3.4 Collaboration with International Cybersecurity Firms
3.4 Market Trends
3.4.1 Adoption of AI and Machine Learning in Security
3.4.2 Shift Towards Managed Security Services
3.4.3 Focus on Data Privacy and Protection
3.4.4 Emergence of Zero Trust Security Models
3.5 Government Regulation
3.5.1 Protection of Personal Information Act (POPIA)
3.5.2 Cybercrimes Act
3.5.3 National Cybersecurity Policy Framework
3.5.4 Sector-Specific Regulations for Telecom Providers
4. SWOT Analysis
5. Stakeholder Analysis
6. Porter's Five Forces Analysis
7. South Africa Cybersecurity in Telecom Networks Market Market Size, 2019-2024
7.1 By Value
7.2 By Volume
7.3 By Average Selling Price
8. South Africa Cybersecurity in Telecom Networks Market Segmentation
8.1 By Type
8.1.1 Network Security
8.1.2 Endpoint Security
8.1.3 Application Security
8.1.4 Cloud Security
8.1.5 Data Security
8.1.6 Identity and Access Management
8.1.7 Others
8.2 By End-User
8.2.1 Telecom Operators
8.2.2 Government Agencies
8.2.3 Enterprises
8.2.4 Small and Medium Businesses
8.3 By Application
8.3.1 Fraud Detection
8.3.2 Network Monitoring
8.3.3 Incident Response
8.3.4 Compliance Management
8.4 By Deployment Mode
8.4.1 On-Premises
8.4.2 Cloud-Based
8.5 By Service Type
8.5.1 Consulting Services
8.5.2 Managed Security Services
8.5.3 Training and Support Services
8.6 By Region
8.6.1 Gauteng
8.6.2 Western Cape
8.6.3 KwaZulu-Natal
8.6.4 Eastern Cape
8.7 By Pricing Model
8.7.1 Subscription-Based
8.7.2 Pay-Per-Use
8.7.3 One-Time License Fee
9. South Africa Cybersecurity in Telecom Networks Market Competitive Analysis
9.1 Market Share of Key Players
9.2 Cross Comparison of Key Players
9.2.1 Company Name
9.2.2 Group Size (Large, Medium, or Small as per industry convention)
9.2.3 Revenue Growth Rate
9.2.4 Customer Acquisition Cost
9.2.5 Customer Retention Rate
9.2.6 Market Penetration Rate
9.2.7 Pricing Strategy
9.2.8 Average Deal Size
9.2.9 Service Level Agreement Compliance
9.2.10 Brand Recognition Score
9.3 SWOT Analysis of Top Players
9.4 Pricing Analysis
9.5 Detailed Profile of Major Companies
9.5.1 Dimension Data
9.5.2 MTN Group
9.5.3 Vodacom Group
9.5.4 Telkom SA SOC Ltd
9.5.5 Darktrace
9.5.6 Check Point Software Technologies
9.5.7 Fortinet
9.5.8 Palo Alto Networks
9.5.9 IBM Security
9.5.10 Cisco Systems
9.5.11 Kaspersky Lab
9.5.12 McAfee
9.5.13 Trend Micro
9.5.14 Sophos
9.5.15 ESET
10. South Africa Cybersecurity in Telecom Networks Market End-User Analysis
10.1 Procurement Behavior of Key Ministries
10.1.1 Ministry of Communications and Digital Technologies
10.1.2 Ministry of State Security
10.1.3 Ministry of Justice and Correctional Services
10.2 Corporate Spend on Infrastructure & Energy
10.2.1 Telecom Infrastructure Investments
10.2.2 Cybersecurity Budget Allocations
10.2.3 Technology Upgrades
10.3 Pain Point Analysis by End-User Category
10.3.1 Telecom Operators
10.3.2 Government Agencies
10.3.3 Enterprises
10.4 User Readiness for Adoption
10.4.1 Awareness of Cybersecurity Threats
10.4.2 Training and Skill Development
10.4.3 Investment in Security Solutions
10.5 Post-Deployment ROI and Use Case Expansion
10.5.1 Performance Metrics
10.5.2 User Satisfaction Levels
10.5.3 Future Use Case Development
11. South Africa Cybersecurity in Telecom Networks Market Future Size, 2025-2030
11.1 By Value
11.2 By Volume
11.3 By Average Selling Price
Go-To-Market Strategy Phase
1. Whitespace Analysis + Business Model Canvas
1.1 Market Gaps Identification
1.2 Business Model Framework
2. Marketing and Positioning Recommendations
2.1 Branding Strategies
2.2 Product USPs
3. Distribution Plan
3.1 Urban Retail Strategies
3.2 Rural NGO Tie-Ups
4. Channel & Pricing Gaps
4.1 Underserved Routes
4.2 Pricing Bands
5. Unmet Demand & Latent Needs
5.1 Category Gaps
5.2 Consumer Segments
6. Customer Relationship
6.1 Loyalty Programs
6.2 After-Sales Service
7. Value Proposition
7.1 Sustainability
7.2 Integrated Supply Chains
8. Key Activities
8.1 Regulatory Compliance
8.2 Branding
8.3 Distribution Setup
9. Entry Strategy Evaluation
9.1 Domestic Market Entry Strategy
9.1.1 Product Mix
9.1.2 Pricing Band
9.1.3 Packaging
9.2 Export Entry Strategy
9.2.1 Target Countries
9.2.2 Compliance Roadmap
10. Entry Mode Assessment
10.1 Joint Ventures
10.2 Greenfield Investments
10.3 Mergers & Acquisitions
10.4 Distributor Model
11. Capital and Timeline Estimation
11.1 Capital Requirements
11.2 Timelines
12. Control vs Risk Trade-Off
12.1 Ownership vs Partnerships
13. Profitability Outlook
13.1 Breakeven Analysis
13.2 Long-Term Sustainability
14. Potential Partner List
14.1 Distributors
14.2 Joint Ventures
14.3 Acquisition Targets
15. Execution Roadmap
15.1 Phased Plan for Market Entry
15.1.1 Market Setup
15.1.2 Market Entry
15.1.3 Growth Acceleration
15.1.4 Scale & Stabilize
15.2 Key Activities and Milestones
15.2.1 Activity Timeline
15.2.2 Milestone Tracking
Research Methodology
Phase 1: Approach1
Desk Research
- Analysis of industry reports from telecommunications regulatory bodies in South Africa
- Review of cybersecurity frameworks and guidelines published by the South African government
- Examination of market trends and forecasts from reputable cybersecurity research firms
Primary Research
- Interviews with cybersecurity experts and consultants specializing in telecom networks
- Surveys conducted with IT security managers in major telecom companies
- Focus groups with industry stakeholders to gather insights on current challenges and solutions
Validation & Triangulation
- Cross-validation of findings through multiple data sources, including government publications and industry reports
- Triangulation of qualitative insights from interviews with quantitative data from surveys
- Sanity checks performed by an expert panel comprising industry veterans and academic researchers
Phase 2: Market Size Estimation1
Top-down Assessment
- Estimation of the overall telecom market size in South Africa as a baseline for cybersecurity spending
- Segmentation of the market by service type, including mobile, fixed-line, and broadband services
- Incorporation of growth rates from the telecommunications sector to project cybersecurity investments
Bottom-up Modeling
- Collection of data on cybersecurity budgets from leading telecom operators
- Analysis of service pricing models and their impact on cybersecurity expenditure
- Estimation of market size based on the number of subscribers and average spend on cybersecurity solutions
Forecasting & Scenario Analysis
- Development of predictive models using historical data on cyber threats and telecom network vulnerabilities
- Scenario analysis based on potential regulatory changes and emerging cybersecurity technologies
- Creation of multiple forecasts (baseline, optimistic, and pessimistic) through 2028
Phase 3: CATI Sample Composition1
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Telecom Network Security Solutions | 150 | Chief Information Security Officers, Network Security Managers |
| Cybersecurity Compliance and Regulations | 100 | Compliance Officers, Legal Advisors in Telecom |
| Incident Response and Management | 80 | Incident Response Teams, IT Security Analysts |
| Emerging Cyber Threats in Telecom | 70 | Threat Intelligence Analysts, Risk Management Professionals |
| Investment in Cybersecurity Technologies | 90 | IT Budget Managers, Procurement Officers in Telecom |
Frequently Asked Questions
What is the current value of the South Africa Cybersecurity in Telecom Networks Market?
The South Africa Cybersecurity in Telecom Networks Market is valued at approximately USD 1.2 billion, reflecting significant growth driven by increasing cyber threats, mobile and internet penetration, and the need for regulatory compliance among telecom operators.