Region:Middle East
Author(s):Dev
Product Code:KRAC4868
Pages:81
Published On:October 2025
By Model Type:
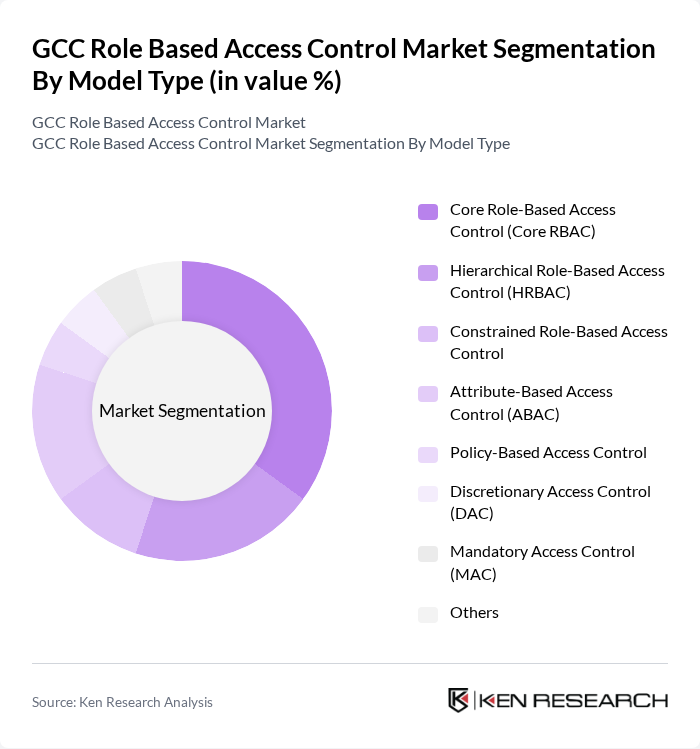
The model type segmentation includes various subsegments such as Core Role-Based Access Control (Core RBAC), Hierarchical Role-Based Access Control (HRBAC), Constrained Role-Based Access Control, Attribute-Based Access Control (ABAC), Policy-Based Access Control, Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Others. Among these, Core RBAC is the leading subsegment due to its simplicity and effectiveness in managing user permissions based on roles within organizations. The increasing complexity of organizational structures and the need for streamlined access management are driving the adoption of Core RBAC solutions, which provide scalability, security, and flexibility for enterprises managing fine-grained access controls. Hierarchical RBAC is also gaining traction as organizations seek to manage role inheritance and delegation more efficiently.
By Organization Size:
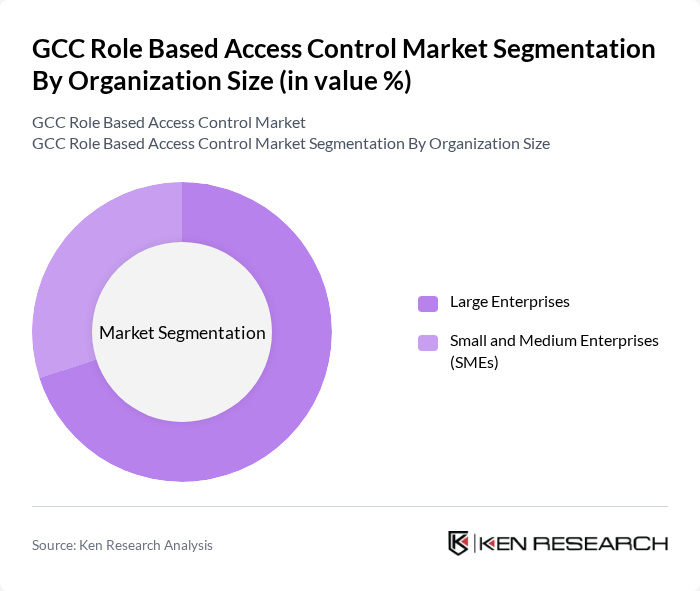
This segmentation includes Large Enterprises and Small and Medium Enterprises (SMEs). Large Enterprises dominate the market due to their extensive operations and the need for comprehensive security solutions to manage access across multiple departments and locations. The increasing focus on regulatory compliance and data protection in large organizations is driving the demand for advanced role-based access control systems, as these entities typically have more complex IT environments and higher exposure to cyber risks. SMEs are also adopting RBAC solutions, but at a slower pace, often due to budget constraints and less complex operational structures.
The GCC Role Based Access Control Market is characterized by a dynamic mix of regional and international players. Leading participants such as Microsoft Corporation, IBM Corporation, Oracle Corporation, Cisco Systems, Inc., Okta, Inc., RSA Security LLC, CyberArk Software Ltd., ForgeRock, Inc., SailPoint Technologies Holdings, Inc., OneLogin, Inc., Ping Identity Corporation, Thales Group, BeyondTrust Corporation, NetIQ Corporation (Micro Focus), Centrify Corporation (now Delinea Inc.), SonicWall Inc., HID Global (Assa Abloy AB), Genetec Inc., WSO2 Inc., ManageEngine (Zoho Corporation) contribute to innovation, geographic expansion, and service delivery in this space.
The future of the GCC role-based access control market appears promising, driven by the increasing emphasis on cybersecurity and regulatory compliance. As organizations continue to adopt digital transformation strategies, the integration of advanced technologies such as artificial intelligence and machine learning into RBAC systems is expected to enhance security measures. Furthermore, the growing trend towards remote work will necessitate more robust access control solutions, ensuring that sensitive data remains protected in a distributed work environment.
| Segment | Sub-Segments |
|---|---|
| By Model Type | Core Role-Based Access Control (Core RBAC) Hierarchical Role-Based Access Control (HRBAC) Constrained Role-Based Access Control Attribute-Based Access Control (ABAC) Policy-Based Access Control Discretionary Access Control (DAC) Mandatory Access Control (MAC) Others |
| By Organization Size | Large Enterprises Small and Medium Enterprises (SMEs) |
| By End-User | Government & Defense Healthcare & Life Sciences Financial Services (BFSI) IT & Telecommunications Manufacturing Retail & E-Commerce Energy & Utilities Transportation & Logistics Education Others |
| By Deployment Model | On-Premises Cloud-Based Hybrid |
| By Component | Solution (Software) Services |
| By Sales Channel | Direct Sales Distributors/Resellers Online Sales |
| By Country | Saudi Arabia United Arab Emirates Qatar Kuwait Oman Bahrain |
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Services RBAC Implementation | 120 | IT Security Managers, Compliance Officers |
| Healthcare Sector Access Control | 100 | System Administrators, Data Protection Officers |
| Government Agency Cybersecurity | 90 | IT Directors, Risk Management Specialists |
| Education Sector RBAC Solutions | 80 | Network Administrators, IT Support Managers |
| Retail Industry Access Management | 110 | Operations Managers, Security Analysts |
The GCC Role Based Access Control Market is valued at approximately USD 1.1 billion, driven by the increasing need for enhanced security measures and the adoption of digital transformation initiatives across various sectors in the region.