About the Report
Base Year 2024Global Security Automation Market Overview
- The Global Security Automation Market is valued at USD 12 billion, based on a five-year historical analysis. This growth is primarily driven by the increasing frequency and sophistication of cyber threats, the need for compliance with regulatory standards, and the rising demand for operational efficiency in security processes. Organizations are increasingly adopting automation solutions to enhance their security posture, reduce response times to incidents, and address the growing complexity of digital environments. The integration of artificial intelligence, machine learning, and big data analytics into security systems further accelerates market adoption by improving threat detection and response capabilities .
- Key players in this market include the United States, China, and Germany. The United States dominates due to its advanced technological infrastructure, significant investments in cybersecurity, and a high concentration of leading security firms. China follows closely, driven by rapid digital transformation, increased adoption of cloud and IoT technologies, and government initiatives to strengthen cybersecurity. Germany's strong industrial base and stringent data protection laws, particularly within the European Union regulatory framework, also contribute to its prominence in the market .
- In 2023, the European Union implemented the Digital Operational Resilience Act (DORA), which mandates that financial entities must ensure their IT security measures are robust and resilient. The Digital Operational Resilience Act, 2023, issued by the European Union, requires financial institutions to adopt comprehensive digital risk management frameworks, conduct regular security testing, and ensure rapid incident response capabilities. This regulation aims to enhance the overall cybersecurity framework within the financial sector, compelling organizations to adopt security automation solutions to comply with the new standards .
Global Security Automation Market Segmentation
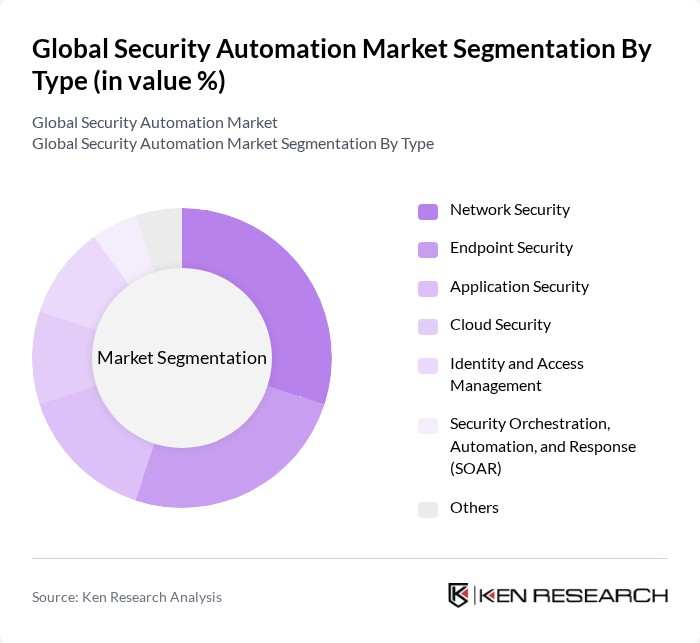
By Type:The market is segmented into various types, including Network Security, Endpoint Security, Application Security, Cloud Security, Identity and Access Management, Security Orchestration, Automation, and Response (SOAR), and Others. Each of these segments plays a crucial role in addressing specific security challenges faced by organizations. Network Security and Endpoint Security remain the largest segments due to the widespread need to protect distributed IT assets and user devices. SOAR platforms are gaining traction as organizations seek to streamline and automate incident response and threat intelligence workflows .
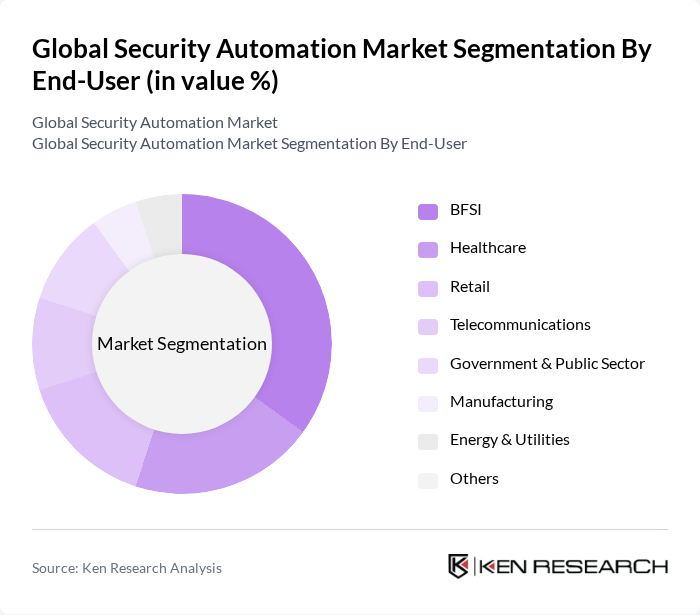
By End-User:The market is segmented by end-users, including BFSI, Healthcare, Retail, Telecommunications, Government & Public Sector, Manufacturing, Energy & Utilities, and Others. Each sector has unique security needs that drive the adoption of automation solutions. BFSI leads due to high regulatory requirements and the critical nature of financial data, while healthcare and retail are rapidly increasing adoption to address rising cyber risks and compliance mandates .
Global Security Automation Market Competitive Landscape
The Global Security Automation Market is characterized by a dynamic mix of regional and international players. Leading participants such as Palo Alto Networks, Fortinet, Check Point Software Technologies, IBM Security, Cisco Systems, Splunk, McAfee, Trend Micro, CrowdStrike, CyberArk, Zscaler, SentinelOne, Darktrace, Rapid7, Tenable, Proofpoint, Okta, Microsoft Security, Google Cloud Security, Amazon Web Services (AWS) Security contribute to innovation, geographic expansion, and service delivery in this space.
Global Security Automation Market Industry Analysis
Growth Drivers
- Increasing Cyber Threats:The global cost of cybercrime is projected to reach $10.5 trillion annually in future, highlighting the urgent need for enhanced security measures. In future, organizations are expected to allocate approximately $150 billion to cybersecurity solutions, driven by the rising frequency of data breaches and ransomware attacks. This escalating threat landscape compels businesses to adopt security automation technologies to protect sensitive data and maintain operational integrity, thereby fueling market growth.
- Demand for Operational Efficiency:Companies are increasingly seeking automation to streamline security operations and reduce response times. In future, organizations are anticipated to invest around $200 billion in operational efficiency initiatives, with a significant portion directed towards security automation. This trend is driven by the need to optimize resource allocation and enhance incident response capabilities, allowing businesses to focus on core activities while ensuring robust security measures are in place.
- Integration of AI and Machine Learning:The integration of AI and machine learning technologies into security automation is transforming the industry. By future, the AI in cybersecurity market is expected to reach $38.2 billion, as organizations leverage these technologies to detect threats in real-time and automate responses. This shift not only enhances threat detection accuracy but also reduces the burden on security teams, driving the adoption of automated security solutions across various sectors.
Market Challenges
- High Implementation Costs:The initial investment required for implementing security automation solutions can be substantial, often exceeding $1 million for large enterprises. In future, organizations may face challenges in justifying these costs, especially in a climate of budget constraints. This financial barrier can hinder the adoption of advanced security technologies, limiting the market's growth potential and leaving businesses vulnerable to cyber threats.
- Shortage of Skilled Professionals:The cybersecurity workforce gap is projected to reach 3.5 million unfilled positions in future, creating significant challenges for organizations seeking to implement security automation. This shortage of skilled professionals hampers the effective deployment and management of automated security solutions, leading to potential vulnerabilities. Companies must invest in training and development to bridge this gap, which can further strain resources and budgets.
Global Security Automation Market Future Outlook
As the landscape of cyber threats continues to evolve, the demand for security automation will likely intensify. Organizations are expected to increasingly adopt advanced technologies, such as AI and machine learning, to enhance their security posture. Additionally, the shift towards cloud-based security solutions will drive innovation and investment in the sector. Companies that prioritize automation and integrate robust security frameworks will be better positioned to mitigate risks and respond effectively to emerging threats in the coming years.
Market Opportunities
- Growth in Cloud Security Solutions:The global cloud security market is projected to reach $12 billion in future, driven by the increasing adoption of cloud services. This growth presents significant opportunities for security automation providers to develop solutions tailored for cloud environments, enabling organizations to secure their data and applications effectively while maintaining compliance with regulatory standards.
- Increasing Demand for Managed Security Services:The managed security services market is expected to grow to $46 billion in future, as organizations seek to outsource their security needs. This trend creates opportunities for security automation vendors to partner with managed service providers, offering integrated solutions that enhance threat detection and response capabilities while reducing operational burdens for clients.
Scope of the Report
| Segment | Sub-Segments |
|---|---|
| By Type | Network Security Endpoint Security Application Security Cloud Security Identity and Access Management Security Orchestration, Automation, and Response (SOAR) Others |
| By End-User | BFSI Healthcare Retail Telecommunications Government & Public Sector Manufacturing Energy & Utilities Others |
| By Deployment Mode | On-Premises Cloud-Based Hybrid Others |
| By Region | North America Europe Asia-Pacific Latin America Middle East & Africa |
| By Security Type | Physical Security Cybersecurity Operational Security Others |
| By Service Type | Consulting Services Managed Services Training and Support Integration & Implementation Services Others |
| By Industry Vertical | Government Manufacturing Energy and Utilities Healthcare BFSI IT & Telecommunications Others |
Key Target Audience
Investors and Venture Capitalist Firms
Government and Regulatory Bodies (e.g., Department of Homeland Security, Federal Bureau of Investigation)
Manufacturers and Producers of Security Automation Solutions
Distributors and Retailers of Security Technologies
Cybersecurity Agencies (e.g., National Cyber Security Centre)
Industry Associations (e.g., Security Industry Association)
Financial Institutions and Banks
Insurance Companies Specializing in Cyber Risk
Players Mentioned in the Report:
Palo Alto Networks
Fortinet
Check Point Software Technologies
IBM Security
Cisco Systems
Splunk
McAfee
Trend Micro
CrowdStrike
CyberArk
Zscaler
SentinelOne
Darktrace
Rapid7
Tenable
Proofpoint
Okta
Microsoft Security
Google Cloud Security
Amazon Web Services (AWS) Security
Table of Contents
Market Assessment Phase
1. Executive Summary and Approach
2. Global Security Automation Market Overview
2.1 Key Insights and Strategic Recommendations
2.2 Global Security Automation Market Overview
2.3 Definition and Scope
2.4 Evolution of Market Ecosystem
2.5 Timeline of Key Regulatory Milestones
2.6 Value Chain & Stakeholder Mapping
2.7 Business Cycle Analysis
2.8 Policy & Incentive Landscape
3. Global Security Automation Market Analysis
3.1 Growth Drivers
3.1.1 Increasing Cyber Threats
3.1.2 Demand for Operational Efficiency
3.1.3 Regulatory Compliance Requirements
3.1.4 Integration of AI and Machine Learning
3.2 Market Challenges
3.2.1 High Implementation Costs
3.2.2 Complexity of Integration
3.2.3 Shortage of Skilled Professionals
3.2.4 Rapidly Evolving Threat Landscape
3.3 Market Opportunities
3.3.1 Growth in Cloud Security Solutions
3.3.2 Expansion of IoT Security
3.3.3 Increasing Demand for Managed Security Services
3.3.4 Rising Awareness of Cybersecurity
3.4 Market Trends
3.4.1 Shift Towards Automation in Security Operations
3.4.2 Adoption of Zero Trust Security Models
3.4.3 Increased Investment in Cybersecurity Startups
3.4.4 Focus on Data Privacy and Protection
3.5 Government Regulation
3.5.1 GDPR Compliance
3.5.2 CCPA Regulations
3.5.3 NIST Cybersecurity Framework
3.5.4 PCI DSS Compliance
4. SWOT Analysis
5. Stakeholder Analysis
6. Porter's Five Forces Analysis
7. Global Security Automation Market Market Size, 2019-2024
7.1 By Value
7.2 By Volume
7.3 By Average Selling Price
8. Global Security Automation Market Segmentation
8.1 By Type
8.1.1 Network Security
8.1.2 Endpoint Security
8.1.3 Application Security
8.1.4 Cloud Security
8.1.5 Identity and Access Management
8.1.6 Security Orchestration, Automation, and Response (SOAR)
8.1.7 Others
8.2 By End-User
8.2.1 BFSI
8.2.2 Healthcare
8.2.3 Retail
8.2.4 Telecommunications
8.2.5 Government & Public Sector
8.2.6 Manufacturing
8.2.7 Energy & Utilities
8.2.8 Others
8.3 By Deployment Mode
8.3.1 On-Premises
8.3.2 Cloud-Based
8.3.3 Hybrid
8.3.4 Others
8.4 By Region
8.4.1 North America
8.4.2 Europe
8.4.3 Asia-Pacific
8.4.4 Latin America
8.4.5 Middle East & Africa
8.5 By Security Type
8.5.1 Physical Security
8.5.2 Cybersecurity
8.5.3 Operational Security
8.5.4 Others
8.6 By Service Type
8.6.1 Consulting Services
8.6.2 Managed Services
8.6.3 Training and Support
8.6.4 Integration & Implementation Services
8.6.5 Others
8.7 By Industry Vertical
8.7.1 Government
8.7.2 Manufacturing
8.7.3 Energy and Utilities
8.7.4 Healthcare
8.7.5 BFSI
8.7.6 IT & Telecommunications
8.7.7 Others
9. Global Security Automation Market Competitive Analysis
9.1 Market Share of Key Players
9.2 Cross Comparison of Key Players
9.2.1 Company Name
9.2.2 Annual Revenue (USD Billion)
9.2.3 Security Automation Revenue (USD Million)
9.2.4 Global Market Presence (Number of Regions Served)
9.2.5 Number of Security Automation Products/Platforms
9.2.6 Customer Retention Rate (%)
9.2.7 Average Deal Size (USD)
9.2.8 R&D Investment as % of Revenue
9.2.9 Product Innovation Rate (New Releases/Year)
9.2.10 Brand Recognition Index (Industry Survey Score)
9.3 SWOT Analysis of Top Players
9.4 Pricing Analysis
9.5 Detailed Profile of Major Companies
9.5.1 Palo Alto Networks
9.5.2 Fortinet
9.5.3 Check Point Software Technologies
9.5.4 IBM Security
9.5.5 Cisco Systems
9.5.6 Splunk
9.5.7 McAfee
9.5.8 Trend Micro
9.5.9 CrowdStrike
9.5.10 CyberArk
9.5.11 Zscaler
9.5.12 SentinelOne
9.5.13 Darktrace
9.5.14 Rapid7
9.5.15 Tenable
9.5.16 Proofpoint
9.5.17 Okta
9.5.18 Microsoft Security
9.5.19 Google Cloud Security
9.5.20 Amazon Web Services (AWS) Security
10. Global Security Automation Market End-User Analysis
10.1 Procurement Behavior of Key Ministries
10.1.1 Budget Allocation Trends
10.1.2 Decision-Making Processes
10.1.3 Vendor Selection Criteria
10.1.4 Contracting Practices
10.2 Corporate Spend on Infrastructure & Energy
10.2.1 Investment Trends in Security Solutions
10.2.2 Budget Prioritization
10.2.3 Long-term Financial Commitments
10.2.4 Cost-Benefit Analysis
10.3 Pain Point Analysis by End-User Category
10.3.1 Security Breaches
10.3.2 Compliance Issues
10.3.3 Resource Limitations
10.3.4 Technology Integration Challenges
10.4 User Readiness for Adoption
10.4.1 Awareness Levels
10.4.2 Training Needs
10.4.3 Infrastructure Readiness
10.4.4 Change Management Strategies
10.5 Post-Deployment ROI and Use Case Expansion
10.5.1 Performance Metrics
10.5.2 User Satisfaction Levels
10.5.3 Scalability of Solutions
10.5.4 Future Investment Plans
11. Global Security Automation Market Future Size, 2025-2030
11.1 By Value
11.2 By Volume
11.3 By Average Selling Price
Go-To-Market Strategy Phase
1. Whitespace Analysis + Business Model Canvas
1.1 Market Gaps Identification
1.2 Value Proposition Development
1.3 Revenue Streams Analysis
1.4 Customer Segmentation
1.5 Key Partnerships
1.6 Cost Structure Analysis
1.7 Competitive Advantage
2. Marketing and Positioning Recommendations
2.1 Branding Strategies
2.2 Product USPs
2.3 Target Audience Identification
2.4 Communication Strategies
2.5 Digital Marketing Approaches
3. Distribution Plan
3.1 Urban Retail Strategies
3.2 Rural NGO Tie-ups
3.3 Online Distribution Channels
3.4 Direct Sales Approaches
4. Channel & Pricing Gaps
4.1 Underserved Routes
4.2 Pricing Bands Analysis
4.3 Competitor Pricing Strategies
4.4 Customer Willingness to Pay
5. Unmet Demand & Latent Needs
5.1 Category Gaps
5.2 Consumer Segments Analysis
5.3 Emerging Trends
5.4 Future Needs Assessment
6. Customer Relationship
6.1 Loyalty Programs
6.2 After-sales Service
6.3 Customer Feedback Mechanisms
6.4 Engagement Strategies
7. Value Proposition
7.1 Sustainability Initiatives
7.2 Integrated Supply Chains
7.3 Customer-Centric Approaches
7.4 Competitive Differentiation
8. Key Activities
8.1 Regulatory Compliance
8.2 Branding Efforts
8.3 Distribution Setup
8.4 Training and Development
9. Entry Strategy Evaluation
9.1 Domestic Market Entry Strategy
9.1.1 Product Mix
9.1.2 Pricing Band
9.1.3 Packaging Strategies
9.2 Export Entry Strategy
9.2.1 Target Countries
9.2.2 Compliance Roadmap
10. Entry Mode Assessment
10.1 Joint Ventures
10.2 Greenfield Investments
10.3 Mergers & Acquisitions
10.4 Distributor Model
11. Capital and Timeline Estimation
11.1 Capital Requirements
11.2 Timelines for Implementation
12. Control vs Risk Trade-Off
12.1 Ownership vs Partnerships
12.2 Risk Management Strategies
13. Profitability Outlook
13.1 Breakeven Analysis
13.2 Long-term Sustainability
14. Potential Partner List
14.1 Distributors
14.2 Joint Ventures
14.3 Acquisition Targets
15. Execution Roadmap
15.1 Phased Plan for Market Entry
15.1.1 Market Setup
15.1.2 Market Entry
15.1.3 Growth Acceleration
15.1.4 Scale & Stabilize
15.2 Key Activities and Milestones
15.2.1 Milestone Planning
15.2.2 Activity Tracking
Research Methodology
Phase 1: Approach1
Desk Research
- Industry reports from global security organizations and market research firms
- Government publications on cybersecurity regulations and compliance standards
- White papers and case studies from leading security automation technology providers
Primary Research
- Interviews with Chief Information Security Officers (CISOs) across various sectors
- Surveys targeting IT security managers and automation specialists
- Focus groups with cybersecurity analysts and threat intelligence experts
Validation & Triangulation
- Cross-validation of findings through multiple industry reports and expert opinions
- Triangulation of data from primary interviews and secondary research sources
- Sanity checks conducted through expert panel discussions and feedback sessions
Phase 2: Market Size Estimation1
Top-down Assessment
- Analysis of global IT security spending trends and growth rates
- Segmentation of the market by industry verticals and geographical regions
- Incorporation of emerging threats and regulatory impacts on security automation
Bottom-up Modeling
- Data collection from leading security automation vendors on product sales
- Estimation of market share based on firm-level revenue and deployment metrics
- Volume and pricing analysis for various security automation solutions
Forecasting & Scenario Analysis
- Multi-variable regression analysis incorporating technological advancements and threat landscapes
- Scenario modeling based on potential regulatory changes and market disruptions
- Development of baseline, optimistic, and pessimistic forecasts through 2030
Phase 3: CATI Sample Composition1
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Services Security Automation | 45 | CISOs, IT Security Managers |
| Healthcare Cybersecurity Solutions | 42 | Compliance Officers, IT Directors |
| Retail Sector Security Automation | 38 | Security Analysts, Operations Managers |
| Government Cyber Defense Strategies | 40 | Policy Makers, Cybersecurity Advisors |
| Manufacturing Industry Security Protocols | 43 | IT Managers, Risk Assessment Officers |
Frequently Asked Questions
What is the current value of the Global Security Automation Market?
The Global Security Automation Market is valued at approximately USD 12 billion, reflecting a significant growth driven by increasing cyber threats, regulatory compliance needs, and the demand for operational efficiency in security processes.