Region:Middle East
Author(s):Shubham
Product Code:KRAB5010
Pages:97
Published On:October 2025
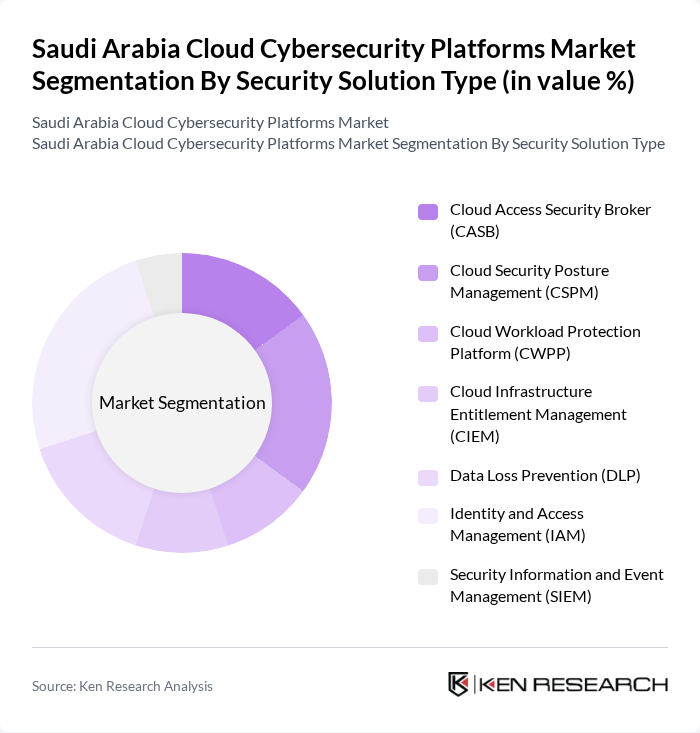
By Security Solution Type:The security solution type segmentation includes Cloud Access Security Broker (CASB), Cloud Security Posture Management (CSPM), Cloud Workload Protection Platform (CWPP), Cloud Infrastructure Entitlement Management (CIEM), Data Loss Prevention (DLP), Identity and Access Management (IAM), and Security Information and Event Management (SIEM). Among these,Identity and Access Management (IAM)is currently the leading subsegment, reflecting the heightened focus on user authentication, privileged access controls, and zero-trust security models in cloud environments. Organizations are prioritizing IAM solutions to address risks associated with unauthorized access, credential theft, and regulatory compliance, especially as remote work and hybrid cloud adoption increase .
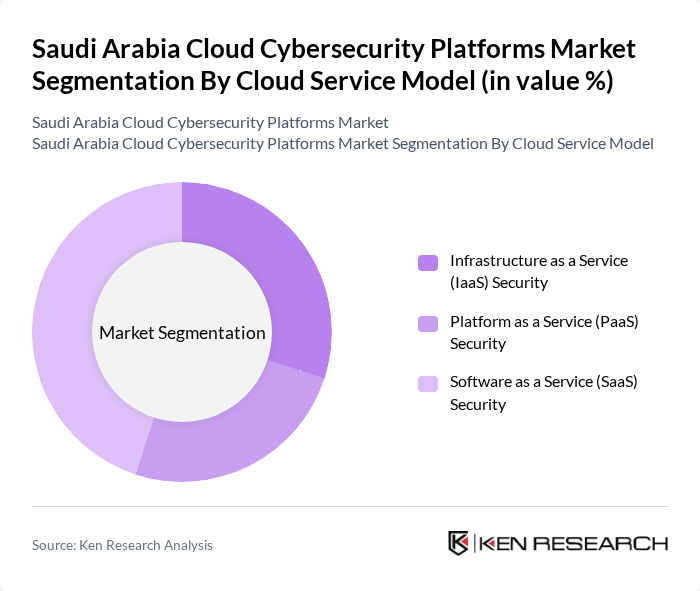
By Cloud Service Model:The cloud service model segmentation includes Infrastructure as a Service (IaaS) Security, Platform as a Service (PaaS) Security, and Software as a Service (SaaS) Security.Software as a Service (SaaS) Securityis the most prominent subsegment, driven by the widespread adoption of SaaS applications in sectors such as banking, healthcare, retail, and government. Organizations are increasingly deploying SaaS solutions to support digital operations, which necessitates advanced security controls for data privacy, access management, and regulatory compliance .
The Saudi Arabia Cloud Cybersecurity Platforms Market is characterized by a dynamic mix of regional and international players. Leading participants such as Palo Alto Networks, Inc., IBM Corporation, Cisco Systems, Inc., Broadcom Inc., Trend Micro Incorporated, Microsoft Corporation, Amazon Web Services (AWS), CrowdStrike Holdings, Inc., Zscaler, Inc., Fortinet, Inc., Check Point Software Technologies Ltd., Proofpoint, Inc., Qualys, Inc., Netskope, Inc., Okta, Inc. contribute to innovation, geographic expansion, and service delivery in this space.
The future of the cloud cybersecurity platforms market in Saudi Arabia appears promising, driven by ongoing digital transformation initiatives and increasing cyber threats. As organizations prioritize data protection, the demand for advanced cybersecurity solutions is expected to rise. Furthermore, the integration of artificial intelligence and machine learning technologies will enhance threat detection capabilities, making cybersecurity more proactive. The collaboration between local firms and global cybersecurity leaders will also foster innovation, ensuring that the market remains resilient against evolving threats.
| Segment | Sub-Segments |
|---|---|
| By Security Solution Type | Cloud Access Security Broker (CASB) Cloud Security Posture Management (CSPM) Cloud Workload Protection Platform (CWPP) Cloud Infrastructure Entitlement Management (CIEM) Data Loss Prevention (DLP) Identity and Access Management (IAM) Security Information and Event Management (SIEM) |
| By Cloud Service Model | Infrastructure as a Service (IaaS) Security Platform as a Service (PaaS) Security Software as a Service (SaaS) Security |
| By Deployment Model | Public Cloud Private Cloud Hybrid Cloud Multi-Cloud |
| By Organization Size | Large Enterprises Small and Medium Enterprises (SMEs) |
| By End-User Industry | Banking, Financial Services and Insurance (BFSI) Government and Public Sector Healthcare and Life Sciences Oil and Gas Telecommunications Manufacturing Retail and E-commerce |
| By Threat Type | Advanced Persistent Threats (APT) Ransomware Protection Data Breach Prevention Insider Threat Management |
| By Pricing Model | Subscription-Based Pay-Per-Use Consumption-Based Hybrid Pricing |
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Sector Cybersecurity | 100 | IT Security Managers, Compliance Officers |
| Healthcare Cloud Security | 60 | Healthcare IT Managers, Data Protection Officers |
| Government Cybersecurity Initiatives | 50 | Government IT Managers, Cybersecurity Policy Makers |
| Retail Sector Cloud Adoption | 40 | IT Managers, E-commerce Directors |
| Telecommunications Cybersecurity Strategies | 70 | Network Security Engineers, Risk Management Executives |
The Saudi Arabia Cloud Cybersecurity Platforms Market is valued at approximately USD 625 million, driven by the rapid adoption of cloud services, increasing cyber threats, and the need for regulatory compliance among businesses in the region.