Region:Middle East
Author(s):Geetanshi
Product Code:KRAB8702
Pages:89
Published On:October 2025
By Type:
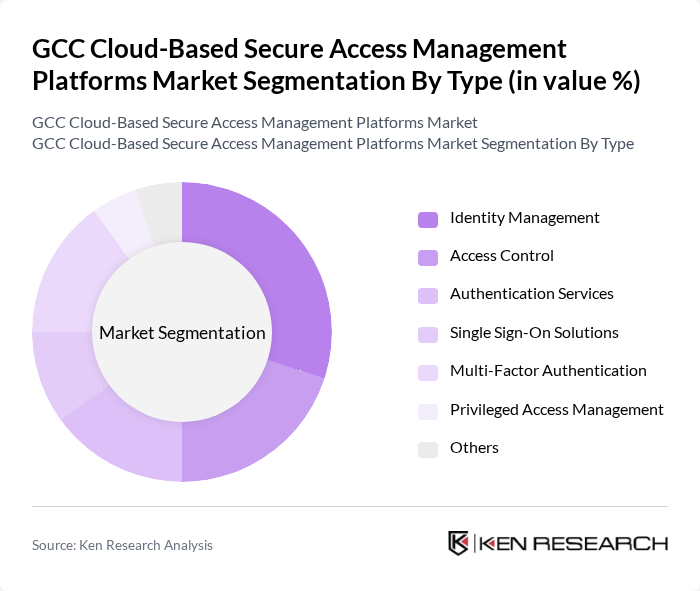
The market is segmented into various types, including Identity Management, Access Control, Authentication Services, Single Sign-On Solutions, Multi-Factor Authentication, Privileged Access Management, and Others. Among these, Identity Management is the leading sub-segment, driven by the increasing need for organizations to manage user identities and access rights effectively. The rise in remote work and digital services has heightened the demand for robust identity management solutions, enabling organizations to ensure secure access to their resources while maintaining compliance with regulations.
By End-User:
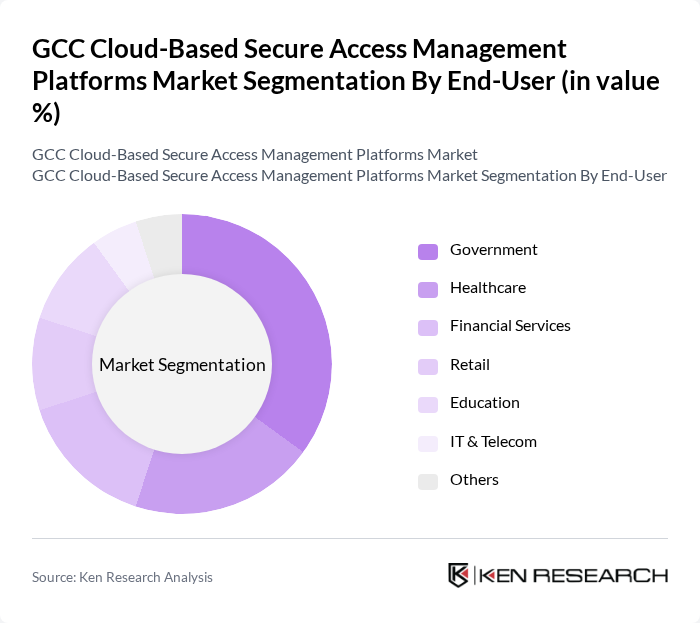
The end-user segmentation includes Government, Healthcare, Financial Services, Retail, Education, IT & Telecom, and Others. The Government sector is the dominant end-user, primarily due to the increasing focus on securing sensitive data and ensuring compliance with stringent regulations. Governments across the GCC region are investing heavily in secure access management solutions to protect critical infrastructure and enhance public sector services, driving the demand for these platforms.
The GCC Cloud-Based Secure Access Management Platforms market is characterized by a dynamic mix of regional and international players. Leading participants such as Okta, Inc., Microsoft Corporation, IBM Corporation, Cisco Systems, Inc., Ping Identity Corporation, RSA Security LLC, ForgeRock, Inc., OneLogin, Inc., CyberArk Software Ltd., SailPoint Technologies Holdings, Inc., Duo Security, Inc., Auth0, Inc., Thales Group, Zscaler, Inc., Centrify Corporation contribute to innovation, geographic expansion, and service delivery in this space.
The future of the GCC cloud-based secure access management platforms market appears promising, driven by the increasing focus on cybersecurity and digital transformation. As organizations continue to embrace remote work and cloud technologies, the demand for secure access solutions will likely rise. Additionally, advancements in artificial intelligence and machine learning will enhance security measures, making these platforms more effective. The market is expected to evolve with innovative solutions that prioritize user experience and compliance with emerging regulations, fostering a secure digital environment.
| Segment | Sub-Segments |
|---|---|
| By Type | Identity Management Access Control Authentication Services Single Sign-On Solutions Multi-Factor Authentication Privileged Access Management Others |
| By End-User | Government Healthcare Financial Services Retail Education IT & Telecom Others |
| By Deployment Model | Public Cloud Private Cloud Hybrid Cloud On-Premises |
| By Industry Vertical | BFSI Manufacturing Energy & Utilities Transportation & Logistics Media & Entertainment Others |
| By Region | Saudi Arabia UAE Qatar Kuwait Oman Bahrain Others |
| By Service Model | Software as a Service (SaaS) Platform as a Service (PaaS) Infrastructure as a Service (IaaS) |
| By Pricing Model | Subscription-Based Pay-As-You-Go Tiered Pricing Others |
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Financial Services Cloud Security | 100 | IT Security Managers, Compliance Officers |
| Healthcare Data Protection | 80 | Healthcare IT Directors, Data Privacy Officers |
| Government Cloud Access Management | 70 | Government IT Administrators, Cybersecurity Analysts |
| Retail Sector Cloud Solutions | 90 | Retail IT Managers, E-commerce Directors |
| Telecommunications Security Solutions | 60 | Network Security Engineers, Operations Managers |
The GCC Cloud-Based Secure Access Management Platforms market is valued at approximately USD 1.2 billion, reflecting significant growth driven by the increasing need for secure access to cloud applications and rising cyber threats across various sectors.