Region:Global
Author(s):Rebecca
Product Code:KRAA2869
Pages:85
Published On:August 2025
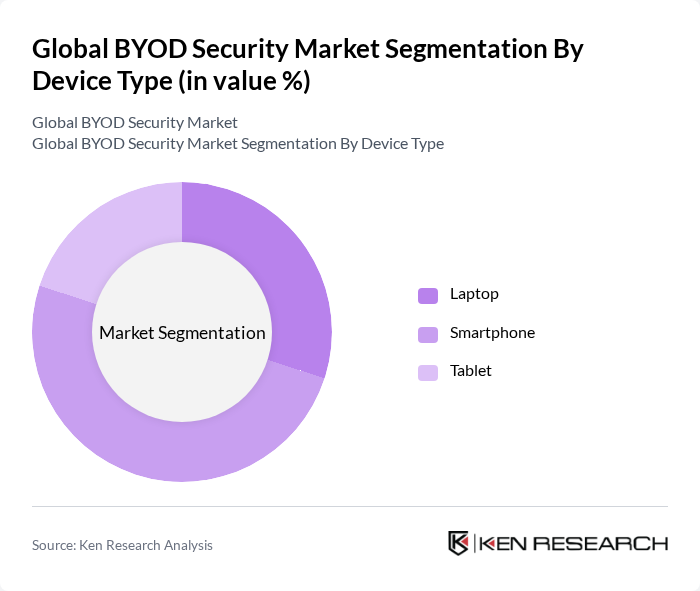
By Device Type:The device type segmentation includes laptops, smartphones, and tablets. Among these, smartphones are the leading sub-segment due to their ubiquitous presence in both personal and professional settings. The increasing reliance on mobile applications for business operations, coupled with the proliferation of mobile malware and phishing attacks, has driven the demand for security solutions tailored for smartphones. Laptops follow closely, as they are essential for remote and hybrid work, while tablets are gaining traction in industries such as healthcare and education, where mobility and ease of use are prioritized .
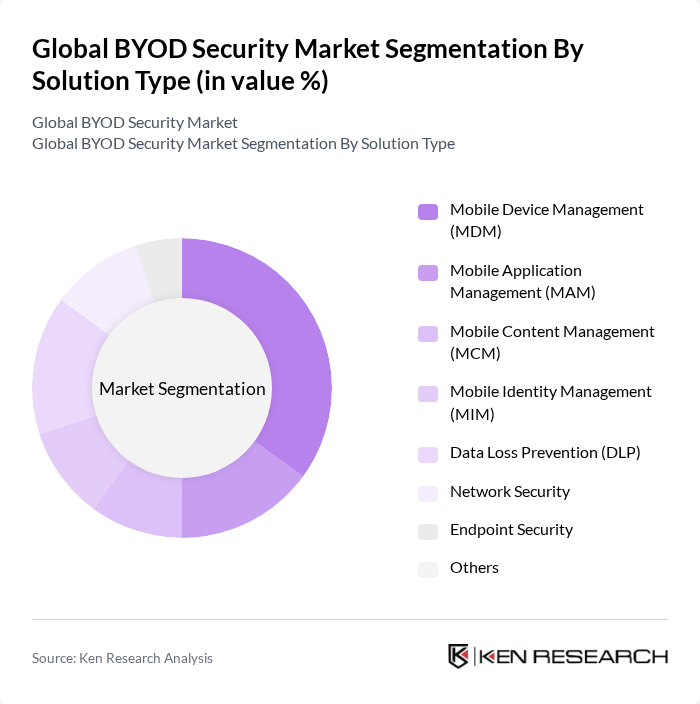
By Solution Type:The solution type segmentation encompasses Mobile Device Management (MDM), Mobile Application Management (MAM), Mobile Content Management (MCM), Mobile Identity Management (MIM), Data Loss Prevention (DLP), Network Security, Endpoint Security, and Others. Mobile Device Management is the dominant solution, as organizations prioritize managing and securing devices accessing corporate data. Data Loss Prevention is also critical, given the increasing incidents of data breaches, while Network Security solutions are essential for protecting organizational networks. The integration of artificial intelligence and machine learning into these solutions is enhancing threat detection and response capabilities, while the adoption of zero-trust frameworks and biometric authentication is further strengthening security postures .
The Global BYOD Security Market is characterized by a dynamic mix of regional and international players. Leading participants such as Cisco Systems, Inc., IBM Corporation, McAfee, LLC, Broadcom Inc. (Symantec Enterprise Division), Palo Alto Networks, Inc., Check Point Software Technologies Ltd., Trend Micro Incorporated, Fortinet, Inc., MobileIron, Inc. (now part of Ivanti), VMware, Inc., Sophos Group plc, Zscaler, Inc., CrowdStrike Holdings, Inc., Bitdefender LLC, RSA Security LLC, BlackBerry Limited, Citrix Systems, Inc., Forescout Technologies, Inc., Aruba Networks (Hewlett Packard Enterprise Development LP), Alcatel-Lucent Enterprise (Nokia Oyj), Microsoft Corporation, Ivanti, GoTo, Logitech International S.A. contribute to innovation, geographic expansion, and service delivery in this space.
The future of the BYOD security market is poised for significant transformation, driven by technological advancements and evolving security needs. As organizations increasingly adopt zero-trust security models, the integration of AI and machine learning will enhance threat detection and response capabilities. Furthermore, the growing emphasis on user behavior analytics will enable businesses to proactively address vulnerabilities, ensuring a more secure environment for remote work and BYOD policies. This proactive approach will be crucial in mitigating risks associated with evolving cyber threats.
| Segment | Sub-Segments |
|---|---|
| By Device Type | Laptop Smartphone Tablet |
| By Solution Type | Mobile Device Management (MDM) Mobile Application Management (MAM) Mobile Content Management (MCM) Mobile Identity Management (MIM) Data Loss Prevention (DLP) Network Security Endpoint Security Others |
| By Deployment Mode | On-Premises Cloud-Based Hybrid |
| By End-User | Small and Medium Enterprises (SMEs) Large Enterprises Government Agencies Educational Institutions Healthcare Organizations Financial Services Others |
| By Industry Vertical | IT and Telecommunications Retail Manufacturing Transportation and Logistics Energy and Utilities Others |
| By Region | North America Europe Asia-Pacific Latin America Middle East and Africa |
| By Security Type | Network Security Endpoint Security Application Security Data Security Others |
| By Pricing Model | Subscription-Based One-Time License Pay-As-You-Go Others |
| Scope Item/Segment | Sample Size | Target Respondent Profiles |
|---|---|---|
| Healthcare Sector BYOD Policies | 100 | IT Security Managers, Compliance Officers |
| Financial Services BYOD Implementation | 80 | Risk Management Directors, IT Administrators |
| Education Sector Device Management | 60 | IT Coordinators, Educational Administrators |
| Retail Industry Security Measures | 70 | Operations Managers, Security Analysts |
| Manufacturing Sector BYOD Challenges | 50 | Plant Managers, IT Support Staff |
The Global BYOD Security Market is valued at approximately USD 73 billion, reflecting significant growth driven by the increasing adoption of mobile devices in workplaces and the need for robust data protection against cyber threats.